Best incident postmortem software for financial services teams in 2026
Updated February 5, 2026
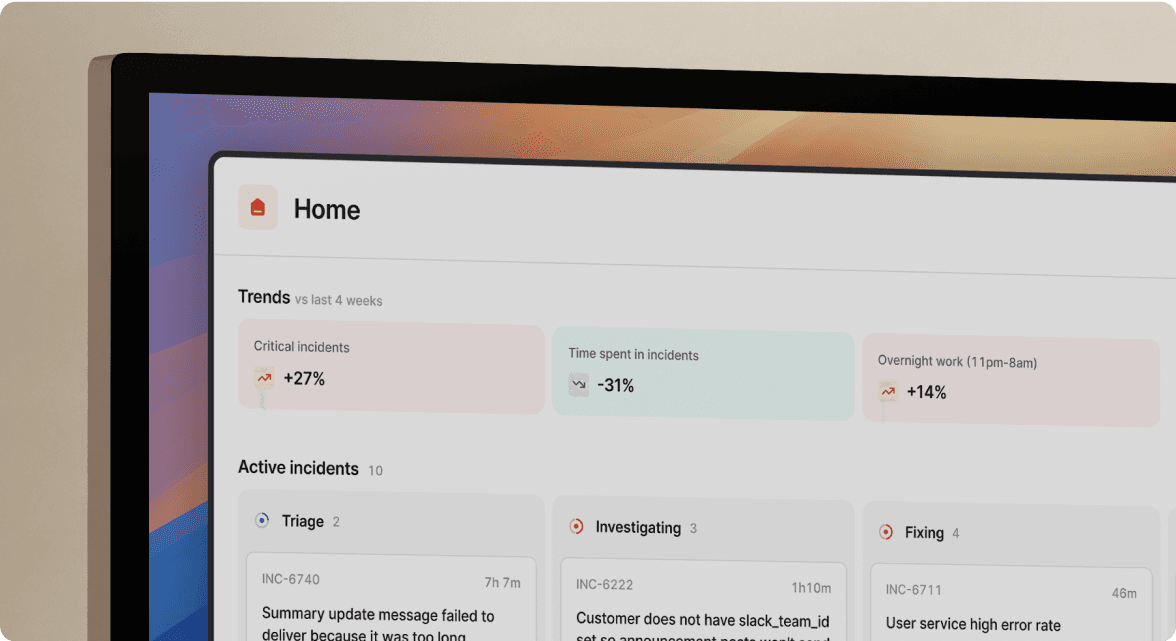
TL;DR: If you run incident response for fintech, you need tools that automate compliance evidence while accelerating resolution. Manual postmortems waste 60-90 minutes per incident reconstructing timelines from scattered Slack threads. We built incident.io to capture timeline data automatically from Slack, satisfy PCI DSS 12.10 and DORA reporting requirements, and reduce postmortem completion to 15 minutes through AI-generated documentation. The platform turns real-time incident chat into immutable audit trails automatically.
Your payment gateway just failed PCI DSS transaction logging for 22 minutes. You resolved the incident, but now you face 90 minutes of postmortem archaeology reconstructing timelines from memory, three Slack channels, and PagerDuty alert history. Your Q2 compliance audit is in six weeks. Your auditor will demand timestamped evidence of who did what, when, and why. This reconstruction tax happens after every major incident, and it costs more than time.
If you operate in financial services, you face unique pressure. DORA requires initial incident notification within 4 hours of determining an incident is major. PCI DSS v4.0.1 Requirement 12.10 mandates documented incident response plans with post-incident reviews. Meanwhile, you waste 60-90 minutes per incident on manual reconstruction.
We built incident.io to eliminate this tax. Our platform automates timeline capture directly from Slack, creating immutable audit trails that satisfy both your CISO's compliance requirements and your team's need for speed.
What postmortem software means in financial services
In financial services, you need postmortem software that creates legally defensible, immutable documentation while maintaining the blameless culture that drives systemic improvements. Standard definitions miss the regulatory nuance: a postmortem is a written record of an incident, but in fintech it's also a compliance artifact subject to audit scrutiny.
Your core requirements include automated timeline generation capturing who did what with precise timestamps, role-based access control for sensitive security incidents, immutable audit trails proving documentation hasn't been tampered with, and integration with compliance monitoring tools like Vanta or Drata. When your platform encrypts data using AES-256 and maintains proper security certifications, postmortems become evidence that survives regulatory examination.
Blameless culture meets regulatory accountability
Financial regulators demand accountability. PCI DSS Requirement 12.10.1 requires documented roles and responsibilities. This creates tension: how do you practice blameless postmortems when regulations legally require identifying who did what?
Focus on process accountability versus human blame. A blamelessly written postmortem assumes everyone involved had good intentions and did the right thing with available information. Document that "Database connection pool reached capacity at 23:34 UTC" and "SRE David initiated rollback at 23:41 UTC" without assigning fault for the capacity gap. Blameless postmortems encourage complete documentation by removing fear, giving regulators the full picture they need.
"The tool aligns itself with your current incident management process instead of forcing you to align your process with a tool. We were able to configure it to guide our Responders to the process without them needing to memorize a bunch of procedures." - Craig C. on G2
Why specialized postmortem tools matter for compliance
Generic documentation tools force you to choose between speed and compliance. Specialized platforms eliminate that choice through automation.
PCI DSS 4.0 postmortem requirements
PCI DSS v4.0.1 Requirement 12.10 mandates a documented Incident Response Plan covering roles, responsibilities, communication strategies, response procedures, and legal reporting obligations. Requirement 12.10.6 specifically requires modifying and improving the incident response plan based on lessons learned.
Here's what that means: every incident affecting cardholder data requires a postmortem documenting what happened, who responded, what worked, what failed, and how you'll prevent recurrence. Requirement 12.10.7 formalizes the process of documenting PAN data found outside documented storage locations.
Manual Google Docs fail this standard because they lack timestamped audit trails. When an auditor asks "Who accessed this sensitive incident documentation and when?", you have no defensible answer.
DORA incident reporting timelines
If you operate in the EU, DORA (Digital Operational Resilience Act) entered application on January 17, 2025, introducing strict incident reporting timelines that make manual postmortems nearly impossible.
DORA requires covered entities to classify incidents based on criticality of affected services, number of affected clients, reputational impact, duration, geographical spread, data losses, and economic impact. Once you determine an incident is "major":
- 4 hours: Initial notification to competent authority (no later than 24 hours from discovery)
- 72 hours: Intermediate report with detailed information
- 1 month: Final report with complete post-incident review
Try reconstructing a compliant timeline from memory and scattered Slack threads in 4 hours. You can't. DORA's real-time response requirements demand tools that capture evidence as incidents unfold.
Before and after automated postmortems
Before specialized tools:
Your alert fires at 11:34 PM. Engineers troubleshoot in three Slack channels. Someone screenshots a Datadog graph. Notes start in Google Doc but stop after 15 minutes when the note-taker shifts to debugging. You resolve at 12:18 AM (44 minutes MTTR). Three days later, you spend 90 minutes reconstructing the timeline from Slack search, PagerDuty history, and interviewing responders who don't remember exact sequences. Your postmortem has timestamp gaps. Your auditor questions accuracy.
After incident.io:
Alert fires at 11:34 PM. We automatically create a dedicated Slack channel, page on-call engineers, and start capturing every message, decision, and role assignment with precise timestamps. Our Scribe transcribes your incident call and extracts key decisions. You resolve at 12:18 AM. Our AI generates an 80% complete postmortem from the captured timeline. You spend 15 minutes refining it, export to PDF, and your compliance system has an immutable audit trail. Total documentation time: 15 minutes versus 90.
"The ease of use and the interface. It's so easy that for reporters across the company it's basically no training and for responders or users customizing workflows it's minimal. After customizing the catalog we could quickly implement the tool and onboard the entire business." - Verified user on G2
Key features you need for financial services
When you evaluate postmortem tools, you need specific capabilities that generic documentation platforms can't provide. Based on working with hundreds of fintech and banking customers, these features separate compliance-ready platforms from inadequate alternatives.
Automated timeline generation with immutable audit trails
When engineers type /inc assign @sarah-devops in Slack, the platform records the role change with timestamp and context. When someone shares a Datadog graph, it's preserved. When the team discusses rollback options, the conversation becomes part of the timeline. Platforms integrate with Slack, monitoring tools, and ticketing systems to automatically capture events as they happen.
Immutability matters for compliance. You can prove to auditors that documentation wasn't edited after the fact because the timeline is built from source system data, not manual entry.
Role-based access control for sensitive incidents
Not every incident should be visible to your entire engineering organization. Security incidents involving customer data breaches, fraud detection failures, or unauthorized access require restricted access.
incident.io supports marking incidents as sensitive and restricting access through private incident types. This implements the role-based access control financial services CISOs require.
Data encryption and compliance certifications
Your CISO will block any tool that doesn't meet security standards. incident.io encrypts data using AES-256 and maintains proper security certifications including documented security controls. Our GDPR compliance addresses European data protection requirements.
We use Slack as our sole authentication mechanism, meaning your existing SSO controls (whether direct Slack auth or SAML through your identity provider) automatically extend to incident.io.
AI-powered postmortem generation
AI SRE capabilities autonomously investigate incidents, correlate data across technology stacks, and identify likely root causes. Our platform drafts complete postmortems including timeline, contributing factors, and follow-ups. You review, tweak, and share in minutes.
AI SRE connects the dots between code changes, alerts, and past incidents to quickly uncover what went wrong and why. This accelerates problem diagnosis significantly.
Top postmortem software for financial teams
Let me compare the platforms financial services teams actually evaluate, focusing on what matters for compliance and velocity.
incident.io: Compliance through Slack-native automation
We built incident.io specifically to solve the compliance-versus-speed paradox. Our Slack-native architecture means incident management happens where engineers already work, eliminating context switching during high-stress incidents.
Key differentiators for financial services:
- Automated audit trails: Every Slack message, role assignment, and decision is captured with precise timestamps
- Private incident types: Sensitive security incidents can be restricted to authorized personnel
- AI-generated postmortems: AI SRE automates investigation and drafts postmortems in minutes
- Compliance-ready exports: Post-incident flow automatically routes postmortems to your system of record
- Service Catalog mapping: Catalog maps incidents to services and teams, auto-populating compliance fields based on service metadata
Pricing for financial services teams:
- Pro plan: $25/user/month base + $20/user/month on-call = $45/user/month total
- Includes AI postmortem generation, private incidents, custom dashboards
- Enterprise: Custom pricing with SAML/SCIM, dedicated CSM
For a 50-person engineering team, expect $27,000/year on Pro plan.
"Their Customer Support team has set a high standard for excellence in customer service. Their professionalism, expertise, and commitment to customer success make them a trustworthy partner." - Verified user on G2
PagerDuty: Transitioning to Jeli for post-incident reviews
PagerDuty's architecture focuses on alerting and on-call management. Their current postmortem capabilities capture timeline data from both PagerDuty alerts and Slack coordination, and include Audit Trail Reporting for configuration changes. However, PagerDuty's Post-Incident Review feature will be discontinued on January 30, 2026, replaced by Jeli's post-incident review product.
While PagerDuty can curate incident timelines from multiple sources, the postmortem creation remains manual - requiring engineers to assemble information from Slack, monitoring tools, and calls into a structured document. Unlike incident.io's AI-first approach, there's no automation to draft the investigation narrative or analysis.
When to consider: You're deeply committed to PagerDuty's alerting and willing to adapt to the Jeli transition in January 2026. Many teams use PagerDuty for alerting and incident.io for coordination and automated postmortem generation. The upcoming product discontinuation is a critical factor for long-term planning in financial services where tool stability matters.
Atlassian: Storage without automation
Atlassian tools serve as storage, not creation platforms. When teams rely on Confluence for manual postmortem creation, engineers spend hours after incidents manually hunting down and copy-pasting chat logs, metrics, and screenshots. Manual data entry introduces errors and memory gaps from delayed documentation.
When to use: As your system of record where AI-generated postmortems are exported, not as your primary creation tool. We integrate with Jira for follow-up task management while maintaining automated timeline capture.
Comparison table: Compliance-critical features
| Feature | incident.io | PagerDuty | Atlassian |
|---|---|---|---|
| Automated timeline capture | Yes, from Slack real-time | Partial, requires curation | No, fully manual |
| Immutable audit trail | Yes, timestamped | Yes, config changes only | No, editable pages |
| AI-generated postmortems | Yes, up to 80% complete | Basic (add-on cost, sunset Jan 2026) | No |
| Private incident types | Yes, RBAC supported | Yes, roles supported | Manual control |
| Time per postmortem | 15-20 minutes | 60-90 minutes | 90-120 minutes |
How to select the right tool for your stack
Your CISO, VP Engineering, and compliance team have different priorities. Use this framework to build consensus across stakeholders.
The compliance-first evaluation checklist
Work through these questions with vendors, demanding specific evidence:
1. Does it create immutable, timestamped audit trails?
Ask to see an exported postmortem with timestamps on every event. Verify timestamps come from source systems (Slack message IDs, alert firing times) rather than manual entry.
2. What security certifications do you hold?
Require documented security controls, GDPR compliance documentation, and data encryption specifications. incident.io provides AES-256 encryption and maintains publicly accessible security documentation.
3. Can you support private incidents for security events?
Test the platform's ability to restrict access to sensitive incidents. Your breach response incidents need access controls that generic tools can't provide.
4. How do you handle DORA reporting timelines?
If you operate in the EU, DORA's 4-hour initial notification requirement demands real-time capture. Ask vendors to demonstrate extracting incident classification data within 4 hours of incident start.
5. What integrations support your compliance stack?
Your postmortems need to flow into compliance monitoring tools (Vanta, Drata), ticketing systems (Jira, Linear), and documentation repositories. Review available integrations and ask about webhook support.
Calculating ROI impact
Here's how to quantify the impact for your business case based on documented MTTR improvements:
Your current baseline:
- Median P1 MTTR: 48 minutes
- Incidents per month: 15
- Downtime cost: Conservative $10,000/hour estimate
- Manual postmortem time: 90 minutes/incident
- Engineer loaded cost: $150/hour
Your projected improvements:
- MTTR reduction: 30-40% (48 min → 30 min, saving 18 min per incident)
- Postmortem time reduction: 75% (90 min → 20 min, saving 70 min per incident)
Annual value calculation:
- Downtime savings: 18 min × 15 incidents × 12 months = 54 hours × $10,000 = $540,000
- Engineering productivity: 70 min × 15 incidents × 12 months = 210 hours × $150 = $31,500
- Total annual value: $571,500
- Platform cost (50 users): $27,000/year
Note: Actual enterprise downtime costs average $540,000/hour, making these estimates conservative.
Schedule a demo to see how we eliminate 90 minutes of manual timeline reconstruction from every incident. See how our post-incident flow automates compliance documentation your auditors actually accept.
"We like how we can manage our incidents in one place. The way it organizes all the information being fed into an incident makes it easy to follow for everyone. The recent addition of on-call allowed us to migrate our incident response stack from PagerDuty and Statuspage to a single tool." - Joar S. on G2
Key terms glossary
Immutable audit trail: Timestamped record of incident events that cannot be altered after creation, providing legally defensible evidence for regulatory audits.
PCI DSS Requirement 12.10: Payment Card Industry Data Security Standard requirement mandating documented incident response plans and post-incident reviews for organizations handling cardholder data.
DORA (Digital Operational Resilience Act): EU regulation effective January 17, 2025, requiring financial entities to report major ICT incidents within strict timelines (4 hours initial, 72 hours intermediate, 1 month final).
Blameless postmortem: Incident review focused on systemic factors rather than individual fault, encouraging honest documentation while maintaining accountability for outcomes.
MTTR (Mean Time To Resolution): Average time from incident detection to full resolution. Automated postmortem tools reduce MTTR by eliminating coordination and documentation overhead.
FAQs

See related articles

incident.io launches PagerDuty Rescue Program
incident.io just launched the PagerDuty Rescue Program, making it easier than ever for engineering teams to ditch their decade-old on-call tooling. The program includes a contract buyout (up to a year free), AI-powered white glove migration, a 99.99% uptime SLA, and AI-first on-call that investigates alerts autonomously the moment they fire.
 Tom Wentworth
Tom Wentworth
Humans aren’t fast enough for 4 9’s
Hitting 99.99% isn't a faster version of what you already do. It's a different problem to be solved: autonomous recovery, dependency ceilings, redundancies, and the discipline to build systems that buy you 15-30 minutes before you're needed at all.
 Norberto Lopes
Norberto Lopes
Who's on call? How Claude helped us calculate this 2,500x faster
A look at how on-call schedules work, and how we made rendering them 2,500× faster — through profiling, smarter algorithms, and some Claude.
 Rory Bain
Rory BainSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization



