Rootly for enterprise: Compliance, governance, and better alternatives
Updated April 3, 2026
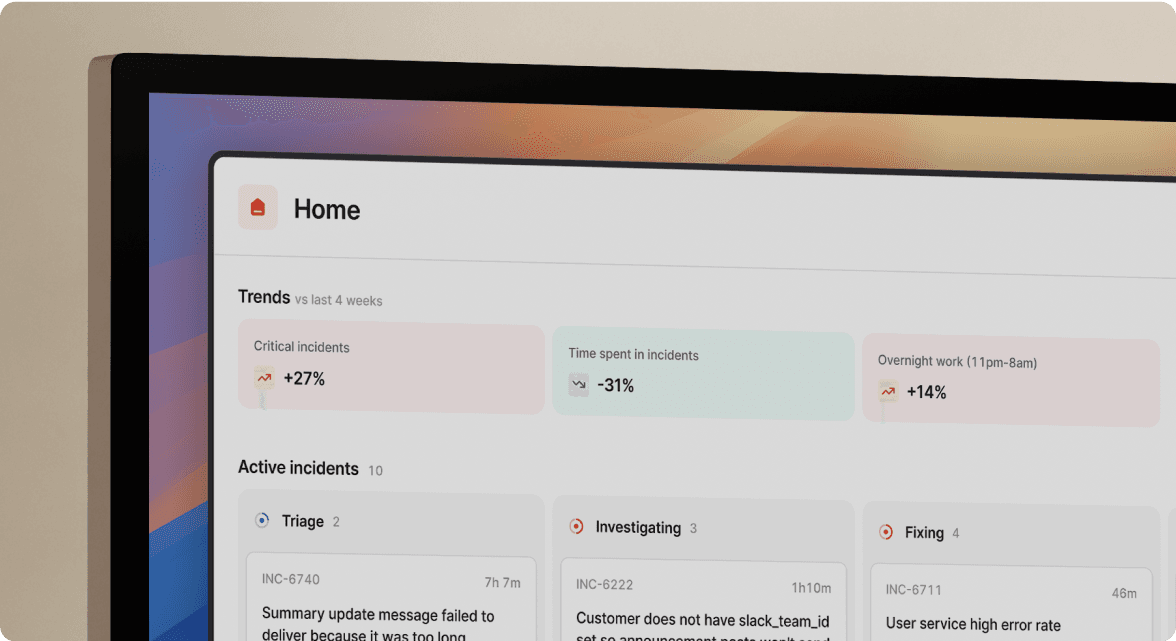
TL;DR: Enterprise teams need automated audit trails, strict RBAC, and SCIM lifecycle management to pass SOC 2 and GDPR audits without slowing incident response. Rootly handles basic incident automation and claims SOC 2 and GDPR readiness, but its public documentation on EU data residency and SCIM availability by plan is sparse. We built incident.io as a Slack-native platform with comprehensive automatic timeline capture, enterprise-grade SCIM and RBAC on the Enterprise plan, and an AI SRE that can reduce MTTR by up to 80% while generating compliance-ready post-mortems automatically.
Access control and change management failures cause most SOC 2 audit exceptions, and the reason has nothing to do with engineering skill. Tool sprawl is the culprit. When your incident response lives across PagerDuty alerts, Slack threads, Google Docs, and a Jira ticket nobody updates consistently, your auditors see four partial records and call none of them complete.
As your engineering team scales, this problem compounds. You need role-based access controls that auto-update when someone leaves, a timeline that builds itself in real time (not one reconstructed from Slack scroll-back three days later), and data partitioning so the security team's incident data stays invisible to product engineering.
This article compares Rootly against enterprise-grade alternatives and shows how to secure your incident data without sacrificing response speed, covering SOC 2, GDPR, SCIM, RBAC, and audit trail quality with the specific gaps you need to test before signing any contract.
What enterprise security and compliance features does Rootly offer?
Rootly's security documentation addresses SOC 2 compliance, along with granular RBAC and automated timeline capture. Here's what the documentation actually delivers on each front.
SOC 2, GDPR, and compliance claims
Rootly holds SOC 2 Type II certification with publicly available trust center resources, but specific attestation details (exact audit window, auditing firm name, or which Trust Service Criteria the audit covered) aren't in public documentation. For a SOC 2 Type II report to satisfy your auditors, you need the audit window (minimum 3 months, though 6 to 12 months is common), not just confirmation that an audit occurred. The SOC 2 framework from AICPA requires controls to operate effectively across that full window, so your security team will need to request the full report directly from Rootly to confirm coverage aligns with your compliance calendar.
On GDPR: Rootly addresses GDPR compliance in their public Privacy Policy, but their services are hosted in the United States with no EU-exclusive data residency option. Personal data is transferred, stored, and processed in the US (and possibly other countries), with international transfers made pursuant to a data processing agreement incorporating standard data protection clauses. If your data processing agreement (DPA) requires EU data residency, Rootly's US-hosted architecture won't meet that requirement, creating a hard blocker for teams under GDPR Article 46 cross-border transfer restrictions.
User lifecycle management and audit trails
Rootly offers SCIM for automated user provisioning, but public documentation doesn't specify which identity providers are supported, how roles are assigned, or whether SCIM requires a specific plan tier. These are gaps worth closing before assuming automated user lifecycle management is available on day one.
On audit trails: Rootly claims every action taken during an incident is recorded in an automated timeline, though whether this captures all event types automatically including role assignments, escalations, Slack thread activity, and call transcriptions or requires manual input for certain events isn't publicly documented. For SOC 2 and ISO 27001 reviewers, the difference between "captures most things" and "captures everything automatically with complete timestamps" is material.
Multi-team incident control with Rootly
Rootly's public documentation describes four organizational controls for RBAC mapped to SCIM groups, workflow specific permissions, private incidents for sensitive situations, and a multi-tenant architecture with per-team alert routing rules.
Key specifics are absent from public documentation: how roles inherit across SCIM group membership, how granular workflow scoping gets for specific teams or incident types, the depth of per-incident visibility controls, and the exact access model for cross-team incident visibility. Before committing, run a proof-of-concept and request a technical disclosure covering these specifics.
Where Rootly falls short for enterprise requirements
While Rootly offers incident management capabilities, enterprise environments may have specific compliance and security requirements that warrant closer evaluation.
The compliance gap: Rootly's public documentation doesn't confirm EU data residency options, so European enterprise customers can't verify where their incident data sits without going directly to the vendor. Teams under GDPR with data transfer restrictions must submit a vendor disclosure request before completing a lawful transfer assessment. If Rootly's answer doesn't align with your DPA requirements, that friction becomes risk.
The audit trail gap: Tool sprawl drives documentation gaps. When Slack threads, PagerDuty alerts, and Rootly timelines capture different slices of the same incident, auditors see three partial records. The post-mortem problem is well-documented in SRE practice: teams must reconstruct timelines from memory and scroll-back after major incidents, and those reconstructions contain gaps that surface during audits. Rootly's public documentation doesn't specify which event types its timeline automation captures call transcriptions, Slack thread context, and third-party alert data aren't listed as automatically captured in available materials. That means you can't determine coverage from documentation alone before an audit surfaces the gaps.
The SCIM gap: Requiring a support ticket to enable SCIM introduces a manual provisioning window. During that window, offboarded engineers may retain access to active incident channels and historical incident data. For SOC 2 CC6.1 (logical and physical access controls), your auditors need evidence that access termination is automated and timely. Your auditors won't accept a support ticket queue as that evidence.
The certification transparency gap: While Rootly holds ISO 27001 and SOC 2 Type II certifications, detailed SOC 2 attestation information (audit window, auditing firm, TSC scope) may require accessing vendor-specific trust center portals rather than being immediately available in standard public documentation. For teams that need to independently assess compliance coverage without direct vendor contact, this additional step can slow procurement evaluations.
incident.io's audit documentation capabilities
incident.io is built so incident coordination happens natively inside Slack, capturing every event in that workflow automatically: messages, role assignments, /inc commands, and call transcriptions, all with timestamps tied to Slack's infrastructure.
Real-world compliance validation: Vanta's experience
Vanta, a trust management platform that helps companies achieve SOC 2, ISO 27001, and other compliance certifications, uses incident.io to maintain audit-ready evidence across every incident. When auditors ask for proof of incident response processes, Vanta's team pulls complete, timestamped records directly from incident.io: who was paged, what actions were taken, when the incident was resolved, and what the post-mortem concluded. No manual reconstruction. No gaps in the audit trail. The evidence exists because incident.io captured it automatically during the incident itself, not after the fact. If a compliance-focused company like Vanta trusts incident.io to underpin its own audit readiness, it's a strong signal that the platform handles the evidence requirements your auditors will ask for.
SOC 2 audit readiness
incident.io holds SOC 2 certification and can provide documentation about our security posture and controls process to support your security team's evaluation during procurement.
Vanta a compliance automation platform that evaluates vendor security as a core business function chose incident.io for their own incident management. When a company whose product is built around security controls selects your platform, that's a stronger signal than any self-reported certification claim.
The takeaway: if your security team needs evidence that incident.io meets enterprise compliance standards, Vanta's adoption is a credible third-party data point alongside the SOC 2 Type II report.
incident.io provides AES-256 encryption at rest and comprehensive automatic timeline capture using our infrastructure that integrates with Slack, all documented on our security page.
SCIM user lifecycle automation
SCIM provisioning is available to automate user lifecycle management with your identity provider. You can automatically provision groups and assign them the appropriate RBAC role in incident.io (custom or base) via the SCIM configuration. SCIM integration is designed to handle deprovisioning, revoking incident.io access when an engineer's identity provider group membership is removed.
Your auditors need to see automated, timely access termination tied to your identity provider for SOC 2 CC6.1. That's exactly what our SCIM integration provides. incident.io also supports Slack Enterprise Grid for organizations running multiple Slack workspaces, configurable through the Slack Enterprise Grid documentation.
Automatic audit logs and DPA compliance
incident.io captures incident updates, pinned Slack messages, /inc commands, role assignments, escalations, and call transcriptions in the incident timeline. The timeline auto-populates as the incident unfolds, so your post-mortem is built from live data, not reconstructed from memory three days after the fact. This matters because GDPR Article 5(2) requires accountability: your incident records need to accurately reflect what happened, not what someone pieced together from scroll-back.
Intercom's engineering team now publishes post-mortems within 24 hours of incident resolution down from 3 to 5 days. The difference: incident.io captures the timeline automatically during the incident, so there's no post-incident archaeology. Every action, update, and decision is timestamped and attributed in real time.
That complete, immutable record is exactly what GDPR Article 5(2) accountability requires. You're not reconstructing what happened from Slack scroll-back three days later. You have a verifiable audit trail the moment the incident closes.
incident.io is designed to support GDPR compliance requirements, and enterprise customers can request information about data processing agreements. The ITSM compliance guide walks through how SOC 2 and GDPR requirements interact in engineering environments and is worth sharing with your legal team during compliance review.
Who controls incident data visibility?
incident.io includes private incidents for security investigations, compliance events, or HR-related situations where you need to restrict information to a specific group. Private incidents allow you to control which team members can view sensitive incident details, even when your broader engineering team shares the same Slack workspace.
Top Rootly alternatives for 2026 SREs
The incident management landscape for 2026 has three distinct categories: the expensive legacy incumbent, the sunsetting platform, and the modern Slack-native alternatives. Here's how each stands on enterprise compliance.
Feature comparison: enterprise compliance and governance
| Feature | incident.io | Rootly | PagerDuty |
|---|---|---|---|
| SOC 2 certification | Documented publicly | Reported as certified | Reported as certified |
| SCIM provisioning | Enterprise plan | Not publicly documented | Available; plan details not public |
| GDPR/data residency | GDPR compliant, DPA available | GDPR compliant per privacy policy, US-hosted data | GDPR compliant |
| Automatic audit timeline | Comprehensive auto-capture, Slack-native | Timeline features available | Audit logging available |
| Private incidents | Yes, Pro plan and above | Yes | Redaction available for any incident |
| Slack architecture | Full lifecycle in Slack | Slack-native | Web-first, Slack integration |
| AI automation | Up to 80% MTTR reduction | AI features available | AI add-on, not core platform |
| Pricing (base + on-call) | $45/user/month Pro plan ($25 base + $20 on-call add-on) | Contact vendor for pricing | Contact vendor for pricing |
ISO 27001 certification status and RBAC granularity vary by vendor and plan. Request written disclosure on both during your procurement evaluation before signing.
PagerDuty: audit-ready but expensive. PagerDuty positions itself as an enterprise-grade platform with compliance certifications and offers EU data residency, which can satisfy regulated industry requirements. It also carries a significant cost premium, with AI features, noise reduction, and runbooks all priced as add-ons to base licensing. The 2026 PagerDuty alternatives guide details migration paths. If your primary compliance requirement is vendor attestation today and budget isn't a constraint, PagerDuty delivers it, but at a cost and complexity premium that most SRE teams at 100 to 500 person companies don't need.
FireHydrant: capable peer competitor. FireHydrant is a peer incident management platform. Evaluate both during a proof-of-concept focused on SCIM depth and timeline capture completeness, since both are strong in the mid-market. Customers consistently report that incident.io's support responsiveness, specifically bugs fixed in hours and feature requests shipped in days via shared Slack channels, differentiates the experience from the category.
Opsgenie: migration is now urgent. Opsgenie reaches end-of-support on April 5, 2027, with no new purchases or trials available since June 4, 2025. Many teams migrating from Opsgenie will move to Jira Service Management, though JSM serves as a general ITSM platform rather than a purpose-built real-time incident response tool. For teams currently on Opsgenie, our Opsgenie migration guide covers the path with tooling to automate the transition.
What to evaluate when choosing an enterprise incident management platform
Before you sign a contract, answer these four questions during your proof-of-concept:
- SOC 2 and ISO 27001 evidence: Don't accept "we're SOC 2 compliant" as a complete answer. Request the Type II attestation report covering Security (mandatory) and any applicable optional Trust Service Criteria (Availability, Confidentiality, Processing Integrity, Privacy), the audit window (minimum 3 months), the auditing firm name, and continuous monitoring evidence (Vanta, Drata, or equivalent). For ISO 27001, request the certificate, scope, and issuing body.
- Data residency controls: Ask explicitly where incident data resides at rest, in which cloud region, and whether you can contractually restrict data to EU infrastructure. Review the DPA before signing. GDPR Article 46 establishes the standard for adequate safeguards on international data transfers, and your legal team will need documented evidence of the transfer mechanisms in place, not just a residency claim.
- SCIM automation scope: Verify which identity providers are supported, whether SCIM is included on your target plan or requires an upgrade, how long deprovisioning takes from IdP removal to access termination, and whether you can map IdP group membership directly to RBAC roles without manual configuration.
- Timeline capture completeness: Run a test incident during your POC and verify the timeline captures every Slack message automatically, includes call transcriptions without manual upload, exports as an audit-ready document with complete timestamps, and that the auto-capture process requires no dedicated note-taker or manual intervention during the incident.
The key takeaway across all four areas: demand evidence, not claims. Every enterprise vendor claims compliance. The ones worth your trust can show you the audit report, the SCIM configuration, and a live demonstration of comprehensive automatic timeline capture in under an hour.
Schedule a demo to see Slack-native audit trails, SCIM configuration, and AI SRE post-mortem generation in a working environment with your own incident scenarios.
Key terms glossary
MTTR (Mean Time To Resolution): The average time from when you detect an incident to when you fully resolve it and restore service. MTTR is the primary operational metric for measuring incident management effectiveness, tracked in incident.io's Insights dashboard.
SCIM (System for Cross-domain Identity Management): An open standard protocol that automates user provisioning and deprovisioning between identity providers (Okta, Azure AD, Google Workspace) and target applications. SCIM is a strong practical control for SOC 2 CC6.1 compliance evidence, enabling automated and timely access termination.
RBAC (Role-Based Access Control): A security model that assigns permissions to users based on their role within an organization rather than individually. In incident management, RBAC determines who can declare incidents, access private incident data, and manage on-call schedules.
Data residency: The requirement that data is stored and processed within a specific geographic jurisdiction. For GDPR-regulated companies, data residency controls document which cloud region holds your incident records, and your DPA must address the transfer mechanisms governing any data that flows outside the EEA.
DPA (Data Processing Agreement): A legally binding contract between a data controller (your company) and a data processor (a vendor like incident.io) that defines how personal data is collected, stored, and used. Required under GDPR for any vendor that processes personal data on your behalf. Your DPA should specify data retention periods, subprocessor lists, breach notification timelines, and transfer mechanisms for data moving outside the EEA. Review your DPA before onboarding any incident management tool that handles user data, system metadata, or on-call engineer contact information.
FAQs

See related articles

Engineering teams in 2027
A forward look at where engineering teams are heading with AI, based on conversations with design partners who are visibly six-to-twelve months ahead of the average. Tailored code agents, MCP gateways, agentic products that talk to each other — most of the picture is already there in pockets, and the rest of the industry is closing the gap fast.
 Lawrence Jones
Lawrence Jones
incident.io launches PagerDuty Rescue Program
incident.io just launched the PagerDuty Rescue Program, making it easier than ever for engineering teams to ditch their decade-old on-call tooling. The program includes a contract buyout (up to a year free), AI-powered white glove migration, a 99.99% uptime SLA, and AI-first on-call that investigates alerts autonomously the moment they fire.
 Tom Wentworth
Tom Wentworth
Humans aren’t fast enough for 4 9’s
Hitting 99.99% isn't a faster version of what you already do. It's a different problem to be solved: autonomous recovery, dependency ceilings, redundancies, and the discipline to build systems that buy you 15-30 minutes before you're needed at all.
 Norberto Lopes
Norberto LopesSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization



