Best incident postmortem software for MSP teams: 2026 breakdown
Updated February 5, 2026
TL;DR: If you run an MSP, you need postmortem software that isolates client data and automates reporting. Generic incident management tools force you into manual sanitization work, risking data leakage across client boundaries. incident.io solves this with its Catalog feature, which lets you define customers as entities and automatically route incidents, status updates, and postmortems to the right client context. This eliminates hours of manual redaction work while maintaining SOC 2-compliant data segregation. If you're managing incidents across multiple customer environments, you need a platform built for multi-tenancy from the ground up.
Managing incidents for one company is challenging. When you're managing them across 50 distinct client environments, you need fundamentally different tooling. When a production issue hits your Client A's infrastructure at 2 AM, you can't afford to spend 45 minutes manually sorting through Slack threads, redacting sensitive data, and reconstructing timelines while your client's systems are down. Yet you're probably still cobbling together PagerDuty for alerting, Slack for coordination, and Google Docs for client-facing reports.
This fragmented approach creates three critical problems: cross-client data leakage risk, hours of manual SLA calculation per incident, and unprofessional documentation that undermines client trust. The root issue is simple. Multi-tenancy in MSP tools is an architecture where a single software instance serves multiple clients while keeping data isolated and configurations tailored for each. Generic incident management platforms assume you have one internal audience. You have external audiences with contractual SLA obligations and strict data privacy requirements.
Why generic postmortem tools fail MSP
You're paying a real, measurable "sanitization tax." Every incident that impacts a client forces you to manually scrub data before you can share the postmortem. Your process typically includes collecting incident timelines from multiple tools, redacting any references to other clients, manually calculating SLA breach timestamps, formatting the report with client branding, and conducting multi-level review to prevent accidental disclosure.
Here's the math: You manage 20 clients and handle 5 incidents per month (100 incidents annually). Each postmortem requires 45 minutes collecting timeline data from PagerDuty, Slack, and monitoring tools, 30 minutes redacting cross-client references and sensitive data, and 15 minutes formatting with client branding and conducting review. That's 90 minutes per incident, or 150 hours annually, which equals 18.75 full working days. At $150 loaded cost per hour, you're burning $22,500 per year on manual postmortem work alone.
The financial risk extends beyond wasted time. A security breach at an MSP can potentially put all its customers at risk, and mishandling sensitive data could result in steep regulatory fines. When Client A's database schema accidentally appears in Client B's incident report, you're looking at potential SOC 2 violations, legal liability, and severe reputational damage.
Strong boundaries are key for security and compliance, as each tenant must have access controls, data segregation, and audit trails to protect against breaches and meet regulations.
Key features to look for in MSP postmortem software
Multi-tenancy and data isolation
True MSP-ready software uses logical separation so your Client A's incident data never intersects with Client B's data, despite operating within the same platform ecosystem. This means catalog-level segregation where you can define customers as distinct entities, automatic field population based on affected customer context, and workflow automation that routes incidents to customer-specific response teams and status pages.
The key differentiator: does the platform require you to manually configure separation, or does it build separation into the core data model? Manual configuration breaks down as you scale from 10 clients to 50 clients. The decentralized and remote nature of MSP operations adds complexity to incident response, and dealing with multi-tenant environments means incidents must be quickly isolated to avoid broader impact.
Look for platforms that let you create custom entity types in a service catalog. When an incident fires, the system should automatically tag it with the affected customer, pull in that customer's SLA tier, and route alerts to that customer's designated response team. For status page updates, look for platforms that support workflow-based automation for their native status pages, but keep in mind that third-party status page integrations may still require manual updates.
Automated SLA reporting and breach tracking
Right now, you're probably tracking SLA metrics manually using spreadsheets to monitor downtime, response times, and incident resolution rates. An SLA is a documented agreement between you, the MSP provider, and your customer, outlining the scope of services, expected performance levels, and repercussions for non-compliance.
You need software that captures precise timestamps for when each incident is created, acknowledged, escalated, and resolved, then automatically compares these against customer-specific SLA thresholds. The platform should generate per-client uptime reports, not just system-wide availability. Your Client A doesn't care that your overall platform uptime was 99.9% if their specific environment was down for 45 minutes during business hours, breaching their 99.5% SLA.
White-labeling and custom branding
For your MSP, incident reports are product deliverables that directly impact client retention. Sending a generic Google Doc with rough SRE notes undermines the professional image you've built. You need platforms that support custom branding with your logo and color scheme, custom domain hosting for status pages, branded email templates for incident notifications, and export formats that maintain your visual identity.
Customer pages give you the ability to provide your customers with a dedicated, authenticated status page, which can be hosted on MSP-specific domains. You should be able to choose between light and dark themes and add your logo for status pages.
"Incident.io stands out as a valuable tool for automating incident management and communication... Another handy feature is its ability to automate routine actions, such as postmortem reports generation." - Vadym C. on G2
Top incident postmortem software for MSPs
| Feature | incident.io | PagerDuty | Jira Service Management |
|---|---|---|---|
| Multi-tenancy support | Service catalog with custom entities | Manual configuration with Teams feature | Requires project-level setup |
| Postmortem completion time | 15 min (AI-drafted) | 60-90 min (manual) | 45-60 min (template-based) |
| Status page per client | Unlimited (Enterprise plan) | Native status pages included | Requires configuration |
| Slack-native workflow | Full incident lifecycle | Bidirectional incident actions | Notifications and actions |
| Pricing (50 users) | $22,200/year (50 users, 30 on-call) | Custom pricing | Bundled with Atlassian suite |
| Setup time to first incident | 2-5 days | 2-4 weeks typical | 4-8 weeks configuration |
incident.io: Best for Slack-native multi-tenant coordination
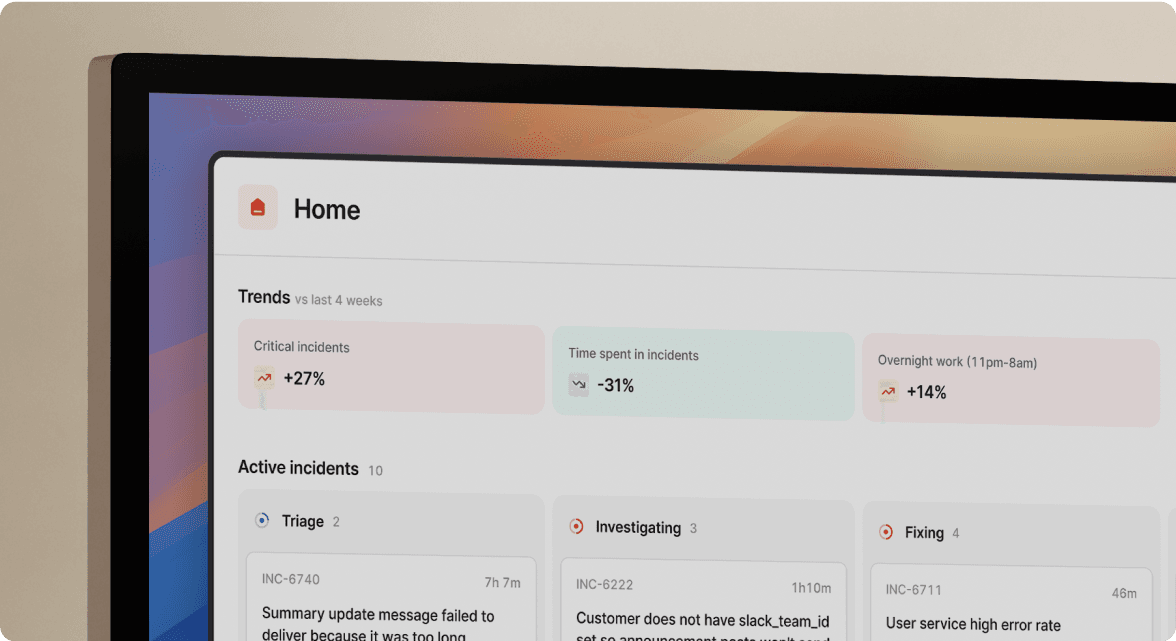
We built incident.io around the premise that MSPs need customer context baked into every incident workflow, not added as an afterthought. The Catalog is a connected map of everything that exists in your organization, available across features like Workflows, Insights, and Triggers.
You can use the incident.io Catalog to track services, teams, product features and anything else, with different categories becoming catalog types. For your MSP, this means creating a "Customer" catalog type with custom attributes like SLA Tier, Technical Contact, Account Manager, and Status Page Link.
When an alert fires, the platform can automatically figure out context using Catalog relationships. If the affected service is Data Pipeline, the affected team is probably Data, and the Catalog can determine this for you. For MSPs, if the affected service belongs to Client A, the system automatically tags the incident with Client A and routes it to Client A's designated response team.
AI SRE tackles the timeline reconstruction work that typically requires 60-90 minutes per incident. The feature captures incident timelines automatically, generates draft postmortems from structured data, and transcribes calls in real time.
In practice, this means postmortem completion time drops from 90 minutes (manual reconstruction from Slack scroll-back, Datadog annotations, and memory) to 15 minutes (reviewing and editing the AI draft). That's an 83% reduction in documentation time. For an MSP handling 100 incidents annually, you reclaim 125 hours per year, which translates to $18,750 in saved labor costs at $150 loaded hourly rate.
"My favourite thing about the product is how it lets you start somewhere simple, with a focus on helping you run incident response through Slack... I'm excited about all the new insights features they're building." - Chris S. on G2
Pricing reality: The Pro plan costs $25 per user per month for incident response, with on-call management costing an extra $20 per user per month. For a 50-user MSP team where 30 engineers are on-call (the rest being account managers, administrative staff, or project coordinators who need incident visibility but not paging), expect $22,200 annually: (50 users × $25/month) + (30 on-call users × $20/month) = $1,850/month.
Critical limitation: The Pro plan includes only one external and one internal status page. If you're managing more than one client environment, you'll need the Enterprise plan for unlimited customer status pages. For MSPs with 10+ clients, this means Enterprise pricing is non-negotiable, pushing your true cost above the $27,000/year baseline. According to incident.io pricing analysis, only the Enterprise plan offers unlimited status pages, which is essential for larger MSP portfolios.
PagerDuty: Best for complex alerting rules
PagerDuty remains the incumbent for sophisticated alert routing with over 370 native integrations and proven alerting reliability. The challenges for MSPs are cost and postmortem complexity. Per-seat pricing escalates quickly as your team grows, and generating client-facing postmortems happens through their GenAI Innovation features, which require additional configuration.
PagerDuty's Slack integration allows you to take action on incidents without leaving Slack, including trigger, acknowledge, escalate and resolve functions, going beyond simple notifications. However, you'll still face manual sanitization work when preparing client-specific reports, and the lack of native customer entity management means you're building multi-tenant separation through manual configuration.
Atlassian (Jira Service Management): Best for existing ecosystem users
If you already use Jira for ticketing and Confluence for documentation, Jira Service Management provides incident management within your existing Atlassian ecosystem. According to Atlassian's documentation, the ChatOps app for Slack lets you receive notifications and perform actions on alerts from Slack channels, going beyond basic notifications.
The downside: JSM feels like a service desk tool adapted for incident response, not purpose-built for it. Real-time response coordination happens in Slack or Microsoft Teams anyway, so you're still context-switching between JSM's web interface and chat during active incidents.
Multi-tenant segregation requires project-level setup. JSM isn't inherently multi-tenant, but you can configure a single instance to support multiple teams by creating separate projects with distinct permissions. There's no native "customer entity" concept, you're building separation through Jira's project hierarchy, which breaks down as client count grows.
How to automate client-facing postmortems
Using incident.io as the reference implementation, here's the workflow for generating client-specific postmortems without manual sanitization.
1. Map clients in your service catalog: Create a custom catalog type called "Customers" with fields for SLA Tier, Status Page Link, Technical Contact, and Account Manager. Each client becomes a catalog entry. Link client catalog entries to the services they use, creating relationship mappings.
2. Tag incidents by customer context: When an alert fires, declare incidents with /inc declare and the system automatically populates customer context based on which service is affected. If Client A's payment processing service triggers an alert, the incident is automatically tagged with Client A's catalog entry.
3. Auto-generate the timeline: The platform automatically captures every action in the dedicated incident Slack channel with precise timestamps. incident.io's Scribe feature transcribes incident calls in real time, extracting key decisions without requiring a designated note-taker.
4. Publish to client-specific status pages: Configure workflows to automatically update incident.io native status pages when incidents are resolved (note: third-party Statuspage integration requires manual updates). The AI drafts the postmortem using captured timeline data, pre-filling 80% of the content. You spend 15 minutes editing, not 90 minutes reconstructing events from memory.
The result: postmortem generation drops from 90 minutes (manual reconstruction from Slack scroll-back, Datadog annotations, and memory) to 15 minutes (reviewing and editing the AI draft). That 75-minute savings per incident compounds across your incident volume.
"Without incident.io our incident response culture would be caustic, and our process would be chaos... Its post-mortem and follow-up tooling is simple, yet detailed, and gives us the structure to quickly share learnings." - Matt B. on G2
Checklist: Evaluating postmortem tools for MSP operations
Use this framework when evaluating vendors:
Data isolation and security:
- Does the platform define customers as distinct catalog entities with automatic segregation?
- Does it maintain separate audit trails per customer to support compliance requirements?
- Can you restrict incident visibility so Client A's team members never see Client B's incidents?
- Does the vendor maintain SOC 2 Type II certification to demonstrate commitment to safeguarding customer environments?
Automation and efficiency:
- Does the system automatically capture incident timelines without manual note-taking?
- Can it generate draft postmortems from structured data, not blank templates?
- Does it calculate SLA metrics per customer automatically based on incident timestamps?
- Can workflows route incidents to customer-specific response teams based on catalog relationships?
Client-facing capabilities:
- Does it support unlimited customer-branded status pages, or are you limited to one or two?
- Can status pages be hosted on your custom domain?
- Does it provide white-labeled email notifications with your branding?
- Can you export postmortems in formats that maintain your visual identity (PDF, Word, Confluence)?
Integration ecosystem:
- Does it integrate bidirectionally with your monitoring tools (Datadog, Prometheus, New Relic)?
- Can it create follow-up tickets in your PSA system (ConnectWise, Autotask) with incident context?
- Does it sync with your documentation platform (Confluence, Notion) for postmortem publishing?
- Can it pull on-call schedules from existing tools if you're not ready to migrate?
Cost structure:
- Is per-user pricing sustainable as you add MSP staff to manage more clients?
- Are critical MSP features (multiple status pages, customer catalog) available in mid-tier plans or locked behind enterprise pricing?
- Does the vendor charge per customer, per incident, or per user? Which model fits your growth trajectory?
- Calculate total cost of ownership: For a 50-person MSP team, incident.io Pro with on-call costs $22,200/year but saves approximately $18,750/year in postmortem labor (125 hours × $150 loaded rate). Net cost: $3,450/year, or $69/year per engineer.
Ready to eliminate the sanitization tax and reclaim 125 hours per year? Schedule a demo to see how the Catalog and customer status pages work for multi-tenant MSP operations.
Key terminology
Multi-tenancy: Architecture where a single software instance serves multiple clients while maintaining isolated data boundaries and tailored configurations for each customer environment.
SLA (Service Level Agreement): Documented contract between MSP and customer specifying service scope, performance targets like 99.9% uptime, response time commitments, and financial penalties for non-compliance.
Sanitization tax: The labor hours you spend manually redacting cross-client references from incident timelines before sharing reports with customers. For MSPs managing 20+ clients, this typically consumes 90 minutes per incident, or 150 hours annually for an MSP handling 100 incidents per year.
Service catalog: Centralized inventory of services, customers, teams, and dependencies that incident management platforms use to automatically populate incident context and route alerts to appropriate responders.
White-labeling: Capability to replace vendor branding with MSP branding in customer-facing materials including status pages, incident notifications, and postmortem reports.
FAQs

See related articles

Engineering teams in 2027
A forward look at where engineering teams are heading with AI, based on conversations with design partners who are visibly six-to-twelve months ahead of the average. Tailored code agents, MCP gateways, agentic products that talk to each other — most of the picture is already there in pockets, and the rest of the industry is closing the gap fast.
 Lawrence Jones
Lawrence Jones
incident.io launches PagerDuty Rescue Program
incident.io just launched the PagerDuty Rescue Program, making it easier than ever for engineering teams to ditch their decade-old on-call tooling. The program includes a contract buyout (up to a year free), AI-powered white glove migration, a 99.99% uptime SLA, and AI-first on-call that investigates alerts autonomously the moment they fire.
 Tom Wentworth
Tom Wentworth
Humans aren’t fast enough for 4 9’s
Hitting 99.99% isn't a faster version of what you already do. It's a different problem to be solved: autonomous recovery, dependency ceilings, redundancies, and the discipline to build systems that buy you 15-30 minutes before you're needed at all.
 Norberto Lopes
Norberto LopesSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization



