Opsgenie vs. JSM: security, compliance & enterprise features compared
Updated March 20, 2026
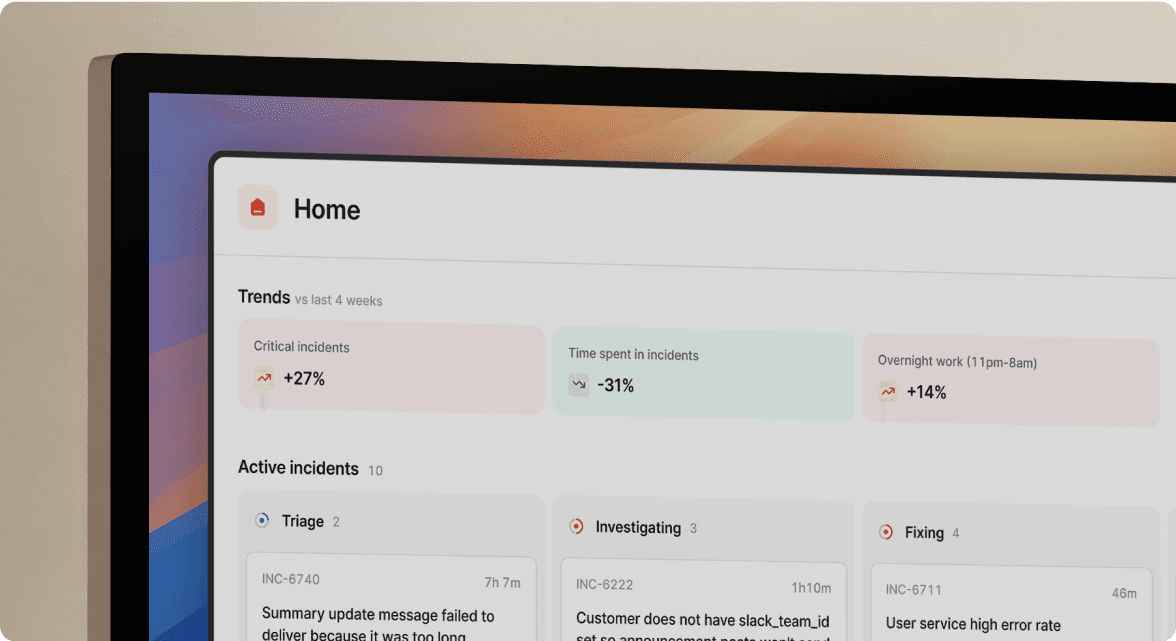
TL;DR: Jira Service Management looks like the natural Opsgenie replacement, but enterprise access controls like SCIM sit behind Atlassian Guard, reportedly adding $4 to $8 per user per month on top of your JSM licenses. Modern alternatives like incident.io include SAML in Enterprise plans without per-user surcharges, provide SOC 2 Type II compliance with automated audit trails, and offer EU data residency to satisfy GDPR requirements. Teams like Etsy (33% MTTR (Mean Time To Resolution) reduction) and Intercom (40% reduction in total incident time) show what a Slack-native platform can deliver compared with the compliance overhead Atlassian migrations create.
The April 2027 Opsgenie sunset is not just a migration project. For teams under SOC 2 Type II or GDPR obligations, it is a compliance risk event. If your replacement platform charges extra to provision users via SCIM, lacks native audit logging, or fails your data residency requirements, you will pass vendor selection and fail the security review, costing your team weeks of rework and budget overruns.
This guide starts with the cost realities of enterprise access control, then walks through SOC 2, GDPR, and audit trail requirements so you can compare Opsgenie, JSM, and incident.io before the April 2027 deadline.
Enterprise access control: SAML, SCIM, and SSO
SAML and SCIM are not optional for enterprise teams because they control your blast radius when engineers leave. SAML lets engineers authenticate through your identity provider (like Okta) without separate passwords. SCIM automates provisioning and deprovisioning, so ex-employees lose access immediately instead of lingering in your on-call rotation for weeks.
During a 3 AM P1 (Priority 1 incident), you need confidence that the person who just joined the incident channel is who they say they are and that your offboarded contractor from last month is not.
The hidden costs of SCIM in Atlassian Guard
Here is the pricing reality for SCIM in the Atlassian ecosystem. Atlassian Guard Standard costs $4 per user per month (annual billing) and Guard Premium costs $8 per user per month. Teams on the Cloud Enterprise plan get Guard Standard bundled in, but Business and Premium plan customers pay extra.
For a 100-person team, Guard Standard adds $4,800 per year. Guard Premium adds $9,600 per year if you need advanced controls like data classification and security policies. For example, if your current Opsgenie spend is approximately $40,000 per year, a JSM migration with Guard Standard could push your all-in incident management cost to around $44,800 or higher before factoring in Confluence for runbooks or Statuspage for customer communication.
Native SAML and SCIM with incident.io
We include SAML in Enterprise plans, with support for identity providers like Okta and other SAML 2.0-compliant systems. There is no separate access management subscription to add. SCIM provisioning is available as a flat-fee add-on rather than a recurring per-user monthly charge, which changes the TCO (Total Cost of Ownership) calculation meaningfully as your team grows.
During a 3 AM incident, SAML-backed SSO (Single Sign-On) means your on-call engineer authenticates once through Okta and immediately has access to the incident channel, service catalog, and runbooks without a separate login. SCIM ensures your on-call rotation only contains active employees, which both reduces security risk and eliminates the confusion of paging engineers who have left the company.
Why security and compliance matter in your Opsgenie migration
Your incident management platform holds your most sensitive operational data: production alerts, service ownership details, on-call schedules, and post-mortem timelines documenting how systems failed and who fixed them. Your CISO cares about this data as much as your engineering team does.
The Opsgenie sunset forces you to answer questions your auditors will ask: Where is incident data stored? Who can access it? Can you produce a complete, tamper-proof timeline of every P0 (Priority 0) incident in the last 12 months? The platform you migrate to must handle this automatically, not as an afterthought.
SOC 2 Type II compliance: Opsgenie, JSM, and modern alternatives
Your auditors expect SOC 2 Type II certification, not Type I. Type I proves your controls were designed correctly on a single day. Type II proves they operated correctly for 3 to 12 months, which is what compliance teams need to sign off on your new incident management platform.
Both Atlassian and incident.io hold SOC 2 compliance. The critical question is not whether they have a certificate but whether the platform makes it easy to generate the evidence your auditors need on an ongoing basis.
What SOC 2 Type II requires and how platforms deliver it
The NIST SP 800-61 framework and ISO/IEC 27035 both recommend that incident response controls be tested and documented over time, not just designed on paper. For SOC 2 Type II auditors, your incident management platform needs to produce:
- Access logs: Who declared the incident, who was paged, and who accessed the incident channel.
- Timeline records: A chronological, tamper-proof record of every action taken during the incident.
- Change tracking: Evidence that only authorized users modified incident severity, roles, and status.
- Data handling records: Proof that sensitive data in post-mortems is retained and deleted according to policy.
JSM can satisfy these requirements, but surfacing a complete, timestamped incident timeline for an auditor requires exporting data from multiple sources: JSM project history, Jira issue activity, Confluence page versions, and Slack message exports if your team coordinates there. Purpose-built platforms generate one exportable timeline per incident by design.
We take a compliance-by-default approach at incident.io. According to our post-mortem compliance guide, we capture every action during an incident automatically: every Slack message in incident channels, all /inc commands (/inc escalate, /inc assign, /inc resolve), role assignments, and timestamps tied to Slack's infrastructure. The result is an append-only audit log, where each entry is timestamped and cannot be altered or deleted without detection, which is exactly what auditors look for when verifying SOC 2 Type II operational effectiveness. Our security FAQs detail the specific controls in place.
"The AI summaries of incidents in Slack is very useful too and startlingly accurate." - Verified user on G2
GDPR and data residency requirements
Your incident data contains personally identifiable information (PII): engineer names, on-call contact details, and customer-facing service descriptions in post-mortems. Under GDPR, this data must be processed lawfully, stored in compliant regions, and subject to defined retention and deletion policies.
Before you sign a contract, answer these three questions:
- Where is my data physically stored?
- Can I choose a specific region, and will that choice hold through contract renewal?
- Does the vendor provide a Data Processing Addendum (DPA) as a standard contract term, or will you need to negotiate it?
Data protection by design in incident workflows
Under GDPR Article 25's data protection by design principle, incident management platforms should protect privacy by default, not through optional add-ons or manual configuration. That means incident channels restrict visibility automatically, post-mortems enforce role-based access, and data minimization happens in the workflow, not as an afterthought.
JSM's native permissions work well for IT service desk tickets (password resets, hardware requests). For real-time production incident response where coordination happens in Slack and timelines span multiple tools, satisfying GDPR's "by default" data minimization requires additional configuration.
We build privacy defaults into the incident workflow at incident.io. Private incidents are available as an opt-in feature that, once enabled, lets responders restrict incident channel visibility to named responders only. Role-based access controls let you configure who views, edits, or exports post-mortems. You get secure defaults and adjust them if needed.
Managing data residency and sovereignty
Atlassian offers data residency in US, EU (Frankfurt and Dublin AWS regions), AU, DE, SG, CA, IN, or CH regions, which covers most sovereignty requirements for multinational teams.
We host incident.io transactional data in GCP's Belgium region (europe-west1), with a hot standby in the Netherlands (europe-west4). For teams operating under EU GDPR who need data to stay in Europe, this meets the requirement. US-based teams should confirm residency requirements with the incident.io sales team before signing.
Making the right choice for your enterprise
If you already use JSM for IT service desk tickets (password resets, hardware requests), keep it there. Add a purpose-built incident response platform for production incidents. JSM follows ITIL workflows built for ticket management, not real-time Slack-native incident coordination.
Consolidating incident coordination into a single Slack-native platform also solves the continuous compliance problem directly. When the auditor asks "show me everything that happened during your October database outage," you should not spend two days reconstructing a story from five sources. All communication sits in one audited space, the timeline captures automatically, and the data model connects alert to resolution to post-mortem in one record.
Teams like Etsy (33% MTTR reduction) and Intercom (40% reduction in total incident time) demonstrate what faster team assembly, automated timeline capture, and reduced context-switching can deliver on a Slack-native platform. The incident.io migration tools for Opsgenie include scripts and API documentation to move on-call schedules, escalation policies, and integrations without starting from scratch. You can also review the ITSM and DevOps stack integration guide if you need to map how incident.io connects with your existing Atlassian tools.
Enterprise compliance checklist: verify before you sign
- SOC 2 Type II report available and covers the last 12 months
- GDPR Data Processing Addendum (DPA) available as a standard contract term
- Data residency region confirmed in writing (US or EU)
- SCIM provisioning pricing confirmed upfront (per-user vs. flat fee)
- Audit logs cover user actions, configuration changes, and incident timelines
- Data retention policy configurable and documented
- Penetration testing results available under NDA
The four bolded items are must-haves before contract signature. The remaining three are for your security review.
| Feature | Opsgenie (sunset Apr 2027) | JSM (Business/Premium) | incident.io (Pro) |
|---|---|---|---|
| SOC 2 Type II | Yes | Yes (Atlassian) | Yes |
| SCIM provisioning | Requires Atlassian Guard (+$4/user/month) | Requires Atlassian Guard (+$4/user/month) | Flat-fee add-on |
| SAML/SSO | Included | Included (Guard required for enforcement) | Included in Enterprise |
| EU data residency | Yes | Yes (Frankfurt + Dublin) | Yes (Belgium + Netherlands) |
| Slack-native workflow | Integration only (web-first /genie commands available but coordination happens outside Slack) | No | Yes |
| Automated audit trail | Partial | Partial | Yes (append-only) |
Schedule a demo to see how incident.io handles enterprise security, compare Atlassian Guard costs for your team size, and walk through the Opsgenie migration plan in 30 minutes. If you want to evaluate on your own timeline, start with our Opsgenie migration tools and documentation.
Key terminology
SCIM (System for Cross-domain Identity Management): An open standard that lets your identity provider (Okta, Azure AD) automatically provision and deprovision user accounts. Without SCIM, ex-employees remain in your incident management platform until someone manually removes them, creating security gaps.
SOC 2 Type II: A third-party audit report that evaluates whether a vendor's security controls operated effectively over a defined period (typically 3 to 12 months). Unlike SOC 2 Type I, which checks control design at a single point in time, Type II confirms consistent execution over time.
MTTR (Mean Time To Resolution): The average time from incident detection to full system restoration, including both technical troubleshooting time and coordination overhead. Reducing coordination overhead (team assembly, context-switching, manual documentation) typically delivers faster MTTR improvements than optimizing the technical fix itself.
FAQs

See related articles

Who's on call? How Claude helped us calculate this 2,500x faster
A look at how on-call schedules work, and how we made rendering them 2,500× faster — through profiling, smarter algorithms, and some Claude.
 Rory Bain
Rory Bain
How it feels to run an incident with AI SRE
For the last 18 months, we've been building AI SRE, and one of the things we've learned is that UX matters more than you think. This week, I used AI SRE to run a real incident, and I walk you through it end-to-end.
 Chris Evans
Chris Evans
What does using AI for post-mortems actually mean?
Everyone is using AI to help with post-mortems now. We've built AI into our own post-mortem experience, pulling your Slack thread, timeline, PRs, and custom fields together and giving your team a meaningful starting point in seconds. But "AI for post-mortems" can mean very different things.
 incident.io
incident.ioSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization



