Best incident postmortem software for compliance and audit teams in 2026
Updated February 16, 2026
TL;DR: Compliance audits fail when incident postmortems live in editable Google Docs or scattered across Slack, Jira, and PagerDuty. SOC 2, ISO 27001, and GDPR require verifiable audit trails with tamper-evident timestamps. The best postmortem software automates evidence collection during incident response, with some organizations reporting reductions of up to 80% in manual documentation work. incident.io creates compliance-ready artifacts automatically by capturing timelines in real-time, while PagerDuty and Jira require manual correlation. For regulated teams, the right platform proves your process to auditors without engineering toil.
When an auditor requests timestamped evidence of how you handled last quarter's P1 incidents, you have minutes to produce a verifiable chain of custody. Most teams scramble through Slack exports, PagerDuty alerts, and Google Doc version histories, only to discover their evidence trail has gaps, edits, and missing context.
We built incident.io to solve this exact problem. Our platform turns your natural Slack workflow into a tamper-evident audit trail automatically. Every message, command, and decision becomes verifiable evidence designed to prevent undetected modification, without requiring dedicated note-takers or post-incident reconstruction. This guide shows you which features matter most for passing SOC 2, ISO 27001, and GDPR audits without slowing down your incident response.
Why compliance audits fail without specialized postmortem software
Your manual incident documentation may struggle to provide a real-time audit trail that meets compliance requirements. Version history in Google Docs or Confluence can be edited or altered without clear traceability, making it difficult for auditors to verify when actions actually occurred. Chat logs, participant lists, and key decision points often go unrecorded when teams must manually reconstruct incidents from memory.
This distinction matters when you face regulatory audits:
- SOC 2's CC7.3 control requires you to demonstrate procedures for responding to security incidents
- ISO 27001's Annex A.16 outlines 7 controls you must implement for information security incident management
- GDPR Article 33(5) states you must document personal data breaches, comprising the facts relating to the breach, its effects, and remedial action taken
You pay for this in real dollars. Failed audits delay sales cycles for enterprise customers who require SOC 2 attestation. Regulatory fines for GDPR violations reach millions. More insidiously, you create toil for your team. Organizations report saving hundreds of hours per audit cycle by automating compliance, with platforms automating up to 80% of manual evidence collection tasks.
Essential features for compliance-ready incident management
Immutable audit trails and tamper-proof logging
You need to understand the difference between a standard incident log and an immutable audit trail because it determines whether your evidence holds up under scrutiny. An incident log is a chronological record that you can manually edit. You can track user activity, but someone can modify the record itself.
Immutable audit logs use cryptographic protection to create append-only records. Once written, these systems are designed to prevent alteration or deletion of past entries without detection. The core difference is your guarantee of integrity. With a standard log, you can't be certain the data hasn't changed. With an immutable log, you can demonstrate a higher level of assurance.
These systems use cryptographic hashing to ensure that once you make an entry, it becomes tamper-evident, made to prevent undetected alteration, even by system administrators. Audit trails enable you to detect threats proactively, perform forensic analysis, and ensure non-repudiation.
"We can allow all business units to customize workflows for their specific process while having a consistent process overall across the company and we can keep track of any setting changes with audit logs going to Datadog." Verified user on G2
Automated evidence collection vs. manual gathering
You'll burn substantial resources on manual evidence collection, including personnel and time. Collecting and organizing evidence manually consumes hours, especially for larger organizations with extensive compliance requirements.
The time savings are dramatic. Research by Secureframe found that 97% of users reduced time spent on compliance tasks, with 76% cutting that time by at least half. Organizations using automated systems report:
- Hundreds of hours saved per audit cycle
- Up to 80% of manual evidence collection automated
- Audit preparation time reduced from months to weeks
Automated systems capture evidence as incidents unfold rather than reconstructing after the fact. By automating the evidence collection process, you save time and resources that would otherwise go to manual tasks like data entry, conducting interviews, and monitoring email communication.
Granular role-based access control and retention policies
Sensitive incidents require controlled access. Security issues, customer data breaches, and financial incidents can't be visible to your entire engineering organization. The separation of functionality between Slack and the website gives you the ability to have rich reporting and compliance controls without cluttering the experience for incident responders.
You should configure role-based access control to ensure the right stakeholders see sensitive incident data while maintaining audit trails of who accessed what and when. This satisfies the principle of least privilege required by most compliance frameworks.
ISO 27001 requires you to assign owners, be clear on actions and timescales, and retain information for audit purposes. Data retention requirements vary by framework and industry, so you should align your retention policies with applicable regulations and internal requirements.
Top postmortem software for compliance and audit teams
| Criteria | Manual postmortems | Automated compliance software |
|---|---|---|
| Immutability | Editable in Google Docs or Confluence | Cryptographically protected, append-only |
| Effort per incident | 60-90 minutes reconstruction | 10-15 minutes review and export |
| Completeness | Depends on memory, often missing context | Captures every action automatically |
| Searchability | Manual keyword search in docs | Indexed, filterable by time/user/action |
| Audit readiness | Requires manual correlation across tools | Export-ready with chain of custody |
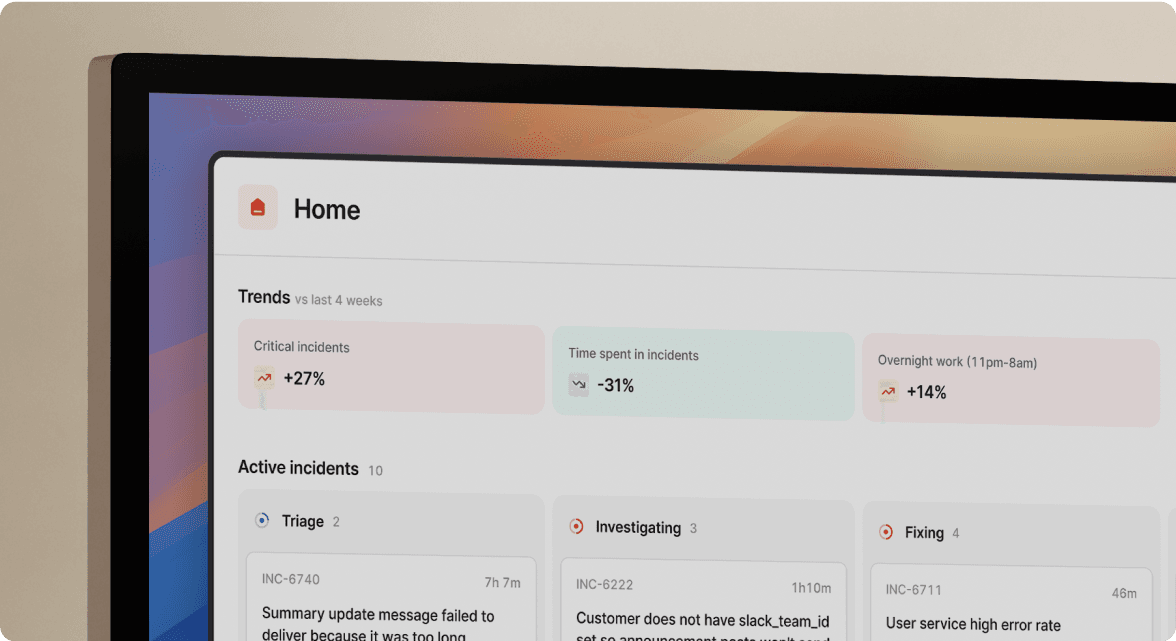
incident.io: Best for automated evidence capture in Slack
We take a "compliance by default" approach at incident.io. Rather than treating audit trails as a separate concern, we capture every action during incident response automatically. Our Slack integration makes reporting and following incidents easy, and our status page works seamlessly with integrations to PagerDuty, Sentry, and Vanta.
When an alert fires from Datadog or another monitoring tool, we automatically create dedicated incident channels, pull in on-call responders, and start capturing timelines. We record every message, slash command (/inc escalate, /inc assign, /inc resolve), and role assignment with immutable timestamps tied to Slack's infrastructure.
Compliance-specific features:
- Private incidents: We support private incidents for security issues requiring confidentiality. You can mark incidents as sensitive and restrict access to specific teams.
- Audit logs: Our comprehensive audit logs track configuration changes and user actions, giving you full visibility into who changed what and when.
- Automated postmortems: We generate postmortems from captured timeline data, turning hours of reconstruction work into minutes of review and refinement.
- Post-incident flows: You can define your post-incident process using customizable flows that ensure consistent documentation for every incident type.
The platform holds SOC 2 certification, demonstrating commitment to security best practices. It provides world-class incident management software integrated into Slack or Microsoft Teams, with security at the core. Data is encrypted using AES-256, and passwords are protected using industry-standard, secure hashing mechanisms.
"The separation of functionality between Slack and the website is extremely powerful. This gives us the ability to have rich reporting and compliance controls in place without cluttering the experience and the workflow for the incident responders... All essential tasks during the incident live phase can be handled or initiated inside Slack." Joar S. on G2
PagerDuty: Best for legacy enterprise alerting
PagerDuty offers postmortems as part of their Business and Enterprise plans, curating a timeline of activity in PagerDuty and Slack. However, you must manually correlate Slack history to identify responders and populate detailed information.
Critical limitation: PagerDuty has announced plans to sunset Postmortems, with removal expected around January 30, 2026. For compliance purposes, PagerDuty's strength remains alerting reliability, but you'll need manual work to bridge alerts with Slack coordination and create audit trails.
Jira Service Management: Best for existing Atlassian suites
Jira Service Management offers automatic postmortem report creation with excellent follow-up tracking. You can track all postmortem actions in Jira, linked as "Priority Action" for root cause fixes or "Improvement Action" for process improvements.
Key limitation: Jira isn't chat-native. Incident timelines live in chat programs like Slack, creating a gap where you must manually copy real-time evidence into Jira tickets.
How to automate your compliance workflow
You can set up a compliant incident management workflow in days, not months, with the right platform.
1. Configure automated channel creation
Ensure every incident starts with a dedicated channel that becomes your single source of truth. When you manually create channels, you introduce delays and inconsistency. Automated channels guarantee every incident follows the same documented process, satisfying SOC 2 requirements for repeatable procedures.
2. Set up role-based permissions for sensitive incidents
Not all incidents should be visible to your entire organization. Security breaches, customer data incidents, and financial issues require restricted access. Configure private incident types with granular permissions that log who accessed sensitive information and when.
We support private incidents that let you mark incidents as sensitive and restrict access to specific teams.
3. Configure auto-export to permanent record systems
Define your post-incident process using the Post-incident Flow to automatically export completed postmortems to Confluence, Notion, or another documentation system. You should configure exports to happen automatically when incidents close, not as a manual follow-up step your team forgets under pressure.
4. Integrate with existing compliance tooling
Connect your incident management platform to your broader compliance stack. Your audit logs should flow into your SIEM or log aggregation system for centralized visibility.
5. Test with sandbox incidents
Before going live, run fake incidents to sandbox your platform. Verify that timelines capture correctly, exports work as expected, and audit logs track all configuration changes.
Selection criteria for regulated industries
When you evaluate postmortem software for compliance purposes, use this checklist to ensure your vendor meets regulatory requirements:
Security certifications:
- Does your vendor hold SOC 2 certification? Request a copy of the report.
- Can you use SAML/SCIM for single sign-on and automated provisioning?
- Do they encrypt your data at rest (AES-256) and in transit?
- Can they provide penetration test results?
Audit trail capabilities:
- Does the platform create immutable, timestamped records automatically?
- Can you export evidence in a readable, non-proprietary format (PDF, Markdown)?
- Are audit logs themselves tamper-proof?
- Can you prove chain of custody for incident evidence?
Access control:
- Does the platform support role-based access control for sensitive incidents?
- Can you restrict who views, edits, or exports incident data?
- Are access attempts logged for audit purposes?
Data retention:
- Can you configure retention policies that align with your compliance requirements?
- Does the platform support automated archival to long-term storage?
- Can you retrieve historical incidents quickly during audits?
Integration ecosystem:
- Does it integrate with your existing monitoring tools (Datadog, Prometheus, New Relic)?
- Can it push follow-up tasks to Jira or Linear automatically?
- Does it export postmortems to your documentation system (Confluence, Notion)?
Vendor compliance:
- Is your vendor GDPR compliant with formal data retention procedures?
- Do they offer data residency options if required by regulation?
- Will they sign a Data Processing Addendum?
Review incident.io's security documentation and trust center to see how we structure transparency.
You shouldn't bolt compliance onto incident management as an afterthought. The best postmortem software for regulated teams automates evidence collection as a natural byproduct of your incident response, turning every Slack message, command, and decision into a tamper-evident audit trail without requiring dedicated note-takers or manual reconstruction.
Your manual documentation creates demonstrable risk. Your editable Google Docs lack verifiable timestamps. Your fragmented evidence across PagerDuty, Slack, and Jira creates gaps auditors will flag. You can save hundreds of hours per audit cycle by eliminating this manual work.
The regulatory requirements are clear. SOC 2's CC7.3 requires demonstrable incident response procedures. ISO 27001's Annex A.16 mandates evidence collection processes. GDPR Article 33(5) requires documenting personal data breaches with facts, effects, and remedial actions.
For teams seeking a platform that delivers compliance by default, run your first incident through our system. See how our automated timeline capture, append-only audit logs designed to prevent undetected modification, and streamlined postmortem generation help reduce the compliance burden. Or schedule a demo to discuss your specific regulatory requirements with our team.
Key terminology
Immutable audit trail: A cryptographically protected, append-only record of events structured so you cannot alter or delete past entries without detection. Essential for proving incident timelines during compliance audits.
SOC 2 Type II: A third-party audit evaluating how effectively you implement and maintain internal controls for data security over 6-12 months. Type II focuses on operational effectiveness, not just design.
Chain of custody: The chronological documentation showing the seizure, custody, control, transfer, analysis, and disposition of evidence. Required to prove incident evidence hasn't been tampered with.
Non-repudiation: The assurance that someone cannot deny the validity of their actions. Immutable audit logs provide non-repudiation by cryptographically binding actions to authenticated identities with tamper-evident timestamps.
FAQs

See related articles

Engineering teams in 2027
A forward look at where engineering teams are heading with AI, based on conversations with design partners who are visibly six-to-twelve months ahead of the average. Tailored code agents, MCP gateways, agentic products that talk to each other — most of the picture is already there in pockets, and the rest of the industry is closing the gap fast.
 Lawrence Jones
Lawrence Jones
incident.io launches PagerDuty Rescue Program
incident.io just launched the PagerDuty Rescue Program, making it easier than ever for engineering teams to ditch their decade-old on-call tooling. The program includes a contract buyout (up to a year free), AI-powered white glove migration, a 99.99% uptime SLA, and AI-first on-call that investigates alerts autonomously the moment they fire.
 Tom Wentworth
Tom Wentworth
Humans aren’t fast enough for 4 9’s
Hitting 99.99% isn't a faster version of what you already do. It's a different problem to be solved: autonomous recovery, dependency ceilings, redundancies, and the discipline to build systems that buy you 15-30 minutes before you're needed at all.
 Norberto Lopes
Norberto LopesSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization



