Best incident postmortem software for security teams: 2026 guide
Updated February 5, 2026
TL;DR: You need postmortem software balancing speed with forensic rigor. The best tools offer private incident channels, immutable audit trails, SIEM integrations, and automated timeline capture. We built incident.io with Slack-native workflows, Private Incidents on the Pro plan, and automated timeline capture. PagerDuty offers battle-tested alerting but complex permissions. Jira requires manual timeline reconstruction. Rootly and FireHydrant target regulated industries. Choose based on your security controls, existing stack, and whether you need real-time forensic capture.
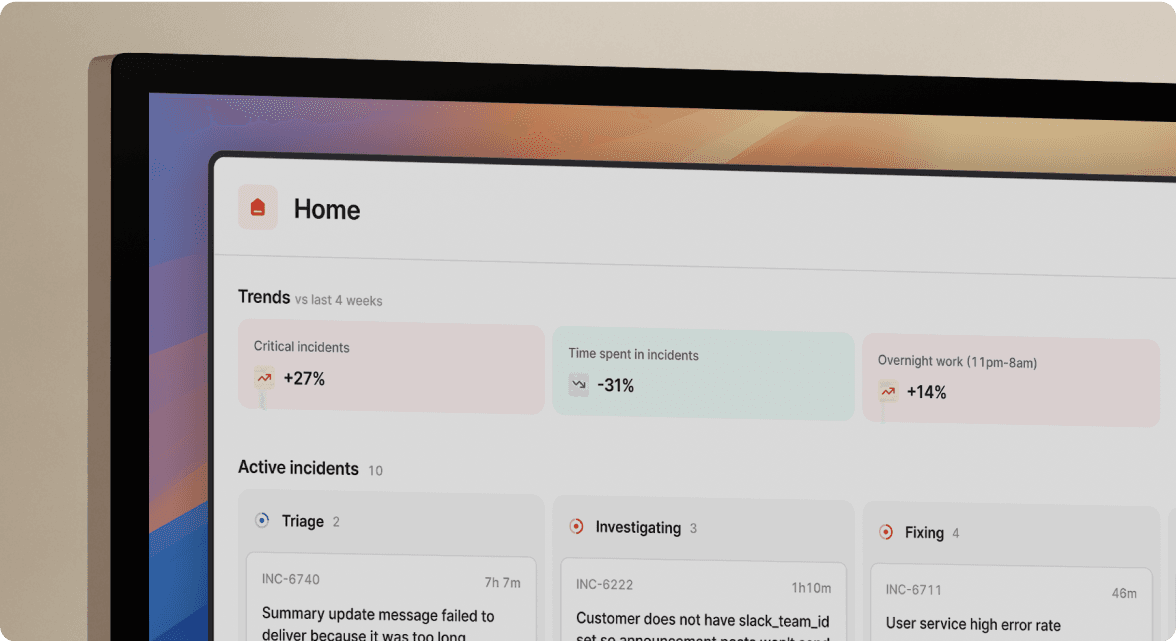
Security incidents create a dilemma: move fast to contain the breach, or preserve forensic evidence for compliance audits. Most teams sacrifice one for the other. We built incident.io to give you both. Slack-native speed with enterprise-grade security controls like Private Incidents and immutable audit logs.The security postmortem challenge: problem, impact, and solutions
The problem
Security incidents require private incident channels to prevent sensitive information from spreading across your workspace. Without private channels, breach details become visible to engineers who don't need to know. Manual timeline reconstruction from edited Slack messages won't satisfy your auditor's chain-of-custody requirements.
The impact
You face three risks: compliance violations from improper data handling ($50k-500k+ in potential fines), incomplete forensic evidence that can't support legal proceedings, and security incidents that take 90+ minutes to document because you're reconstructing timelines from memory instead of captured data.
Quick fix
Use your platform's private incident feature immediately when declaring security events. If your current tool lacks this, create a separate private Slack channel manually and document in a shared doc with edit tracking enabled. Lock down access to need-to-know personnel only.
Long-term approach
Implement automated timeline capture that creates immutable audit trails as incidents happen. Choose tools offering native SIEM integration, RBAC for granular access control, and SOC 2 Type II certification. Establish clear runbooks defining when to mark incidents private. Train incident commanders on forensic documentation requirements.
How we solve this
We designed Private Incidents to solve exactly this. You mark an incident private with one command or toggle. The channel becomes invitation-only. Our AI captures every message, command, and decision with immutable timestamps. When you type /inc resolve, you get a forensically sound postmortem citing dozens of timeline events, not a blank Google Doc.
Implementation steps
- Enable Private Incidents from Settings > Security (Pro plan required)
- Train incident commanders to use
/inc private truewhen declaring security events - Define which incident types require privacy in your runbooks (credential leaks, data breaches, security vulnerabilities)
- Configure SIEM integrations so alerts auto-populate incident timelines
- Export your first automated postmortem and validate it meets your compliance requirements
![Security incident postmortem workflow with forensic controls][image_security_postmortem_workflow]
What defines security-focused incident postmortem software?
Security incident postmortems differ fundamentally from standard reliability postmortems. Standard incidents prioritize speed. Security incidents require forensic integrity and confidentiality.
We've seen this tension play out hundreds of times. Your CISO must answer auditors with immutable evidence. Your legal team needs chain of custody. You must contain sensitive details from the broader organization. A data breach postmortem visible in your company's #general Slack channel is a compliance nightmare.
Standard SRE tools optimize for coordination speed and assume everyone should see everything. Security tools must optimize for confidentiality, integrity, and availability simultaneously. Manual Google Docs that anyone can edit break chain-of-custody requirements because they lack immutable timestamps and audit trails.
The best security-focused postmortem software captures forensic data automatically, enforces strict access controls, integrates with your SIEM for ground-truth alert data, and generates immutable timelines that auditors trust.
The role of incident forensics and chain of custody
In digital forensics, chain of custody means "a process that tracks the movement of evidence through its collection, safeguarding, and analysis lifecycle by documenting each person who handled the evidence, the date/time it was collected or transferred, and the purpose for the transfer."
For security incidents, this translates to capturing every action, decision, and status change with immutable timestamps and attribution. We've seen manual postmortem processes break this chain repeatedly. When you reconstruct a timeline three days after resolution by scrolling through Slack threads, you're relying on human memory and edited messages.
We solved this with automated timeline capture. Our AI SRE captures every Slack message, /inc command, role assignment, and call transcription as events happen. When someone posts "Restarted pods at 3:14 AM," that's logged with timestamp and attribution. When Scribe joins your incident call, it transcribes conversations automatically and flags key decisions.
"Without incident.io our incident response culture would be caustic, and our process would be chaos. It empowers anybody to raise an incident and helps us quickly coordinate any response across technical, operational and support teams." - Matt B. on G2
The timeline is immutable. You can't retroactively claim you escalated to the security team 10 minutes earlier than you actually did. For security teams facing SOC 2 audits or legal discovery, this automated evidence collection is the difference between a 15-minute postmortem export and a week of manual reconstruction.
Key features you must evaluate
When evaluating postmortem software for security incidents, your RFP must address five non-negotiable requirements. These aren't nice-to-haves, they're the difference between passing your next compliance audit and explaining to your CISO why sensitive breach details leaked to the engineering team.
SIEM integration and data ingestion capabilities
When evaluating SIEM integration, ask three questions: Does alert data flow automatically into timelines? Can you audit the exact system state at incident start? Do you need to manually copy-paste from your monitoring dashboard?
We built native integrations with Datadog, Splunk, PagerDuty, and Panther so alerts auto-create incidents and populate timelines without manual entry. You get the triggering metric, threshold breach, and system state automatically.
PagerDuty's postmortem feature curates timelines by linking incidents and Slack channels. Note that PagerDuty is deprecating this feature, with removal scheduled for January 30, 2026. The platform focuses primarily on alerting rather than postmortem documentation.
Jira Service Management requires manual effort. You must copy alert data from your SIEM into Jira tickets. Atlassian's incident management documentation instructs teams to "note observations as incidents happen" because automated ingestion is limited.
Rootly acts as a central hub that ingests alerts from any source through native integrations and generic webhooks, with strong focus on security tool integration.
Audit logging and immutable timelines
In our conversations with security teams preparing for SOC 2 audits, the question we hear most is: "Can you prove no one edited this timeline after the incident?" If your platform allows post-hoc edits without cryptographic signatures, the answer is no.
We capture everything automatically, every Slack message in the incident channel, every /inc escalate command, every role assignment, with immutable timestamps. Our AI Scribe joins your Zoom calls and transcribes decisions like "We're rolling back to version 2.4.1" without requiring a designated note-taker.
"The 1-click post-mortem reports - this is a killer feature, time saving, that helps a lot to have relevant conversations around incidents (instead of spending time curating a timeline)." - Adrian M. on G2
PagerDuty provides audit logs in pagerduty_audit_logs tables collecting administrative changes. But, timelines can be manually edited during postmortem creation, which may not satisfy strict forensic requirements.
Jira Service Management generates an automatically created incident timeline showing status changes and assignments. The limitation is that teams must manually note observations as they happen, and standard Jira audit logs allow users with appropriate permissions to edit tickets.
Rootly emphasizes that every action taken during an incident is automatically logged, generating a complete, unalterable audit trail within their timeline.
Role-based access control and private incidents
This is the crucial security differentiator. When you discover a potential data breach, you cannot have the incident details broadcasting to your entire engineering Slack workspace.
We built Private Incidents specifically for this requirement. You can mark incidents as private when creating them. Only people in the private incident's #inc-... channel have access, and the incidents are undiscoverable by users not already invited. Admins opt-in from Settings > Security, and you can convert incidents from public to private mid-incident. This feature is available on the Pro plan.
PagerDuty handles privacy primarily through Slack channel member restrictions. When closing a private incident, only users who were members of the private channel can be added as Post-Incident Review Owners.
Jira Service Management offers Issue Security Schemes to restrict access to sensitive information. However, configuring these schemes correctly during a high-velocity security incident is complex, and Jira permissions are notoriously difficult to manage.
Rootly provides granular RBAC allowing you to define specific permissions for different roles such as Incident Commander, Comms Lead, or Engineer.
Top incident postmortem software for security teams
The following evaluation covers five platforms, assessed specifically for security incident handling. Each offers SOC 2 Type II certification, but their approaches to forensics, access control, and automation differ significantly.
incident.io: Slack-native with enterprise security controls
We built incident.io to be the secure choice for engineering teams wanting both speed and compliance. Our Slack-native architecture means the incident lifecycle runs primarily in Slack channels using slash commands, with web dashboard access for detailed management and analytics. No context-switching during active security incidents when every second counts.
Key security features:
- Private incidents: Available on Pro plan, instant conversion to invitation-only with undiscoverable channels
- Automated forensic capture: Every Slack message, command, role assignment, and call transcription logged with immutable timestamps
- AI-powered postmortem generation: AI SRE handles up to 80% of incident response, drafting complete postmortems from captured timeline data
- SIEM integrations: Native connections to Datadog, Splunk, PagerDuty, Panther
- Compliance: SOC 2 compliance certified, GDPR compliant, offers SAML/SCIM on Enterprise
"Great automation across multiple tools, such as Google Suite, PagerDuty and Atlassian. Very easy to configure, and making on-the-fly changes is simple. Excellent post-mortem workflow that guides you through the steps from start to finish." - Verified user on G2
Best for: Security teams wanting Slack-native workflows with granular access controls and automated forensic capture. Ideal for 50-500 person companies balancing SRE velocity with CISO compliance requirements.
Watch out for: The opinionated chat-native design means the platform is optimized for Slack and Microsoft Teams. While incident.io supports both platforms with automated workflows and AI integrations, organizations not using either chat platform may find limited value. On-call pricing as an add-on can surprise buyers.
PagerDuty: Battle-tested alerting platform
PagerDuty is the incumbent platform, known primarily for alerting and on-call management. The platform offers over 370 native integrations with comprehensive alert management capabilities.
Key security features:
- Audit logs: Comprehensive logging of administrative changes and user activities
- Alert aggregation: Integration hub with hundreds of tools including major SIEM platforms
- Compliance: SOC 2 Type II, FedRAMP Low Impact, ISO 27001
Best for: Organizations already invested in the PagerDuty ecosystem for alerting who need strong integration capabilities. Enterprises requiring FedRAMP or extensive third-party integrations.
Watch out for: Postmortems feature has been deprecated as of January 30, 2026. Pricing escalates quickly with add-ons.
Jira Service Management: Atlassian ecosystem integration
Jira Service Management is the natural choice for Atlassian shops, offering incident management workflows integrated with existing Jira projects.
Key security features:
- Issue security schemes: Role-based access controls to restrict sensitive ticket visibility
- Automated timeline generation: Status changes, assignments, and linked changes populate automatically
- Asset management: Native capabilities help understand dependencies
Best for: Teams already standardized on Atlassian tools (Jira, Confluence) who need incident workflows integrated with existing service desk operations.
Watch out for: Manual processes dominate. Teams must manually note observations as incidents happen. Complex permission schemes can be misconfigured during high-velocity incidents. The platform is fundamentally a ticketing system, not purpose-built for real-time incident forensics.
Rootly: Compliance-first for regulated industries
Rootly targets regulated teams in healthcare, financial services, and other industries where compliance monitoring is critical.
Key security features:
- Granular RBAC: Define permissions for specific incident roles with identity provider integration
- Comprehensive audit logs: Every action automatically logged in an unalterable timeline
- Compliance support: Explicit support for GDPR, CCPA, HIPAA, and DORA regulations
Best for: Security teams in regulated industries needing explicit compliance workflow support. Strong choice for teams wanting to automate security incident response checklists.
FireHydrant: Runbooks-as-code with structured workflows
FireHydrant approaches incident management through structured runbooks, emphasizing checklist-driven responses.
Key security features:
- SAML authentication: Leverage identity provider's existing access controls
- SOC 2 type II compliance: Achieved September 2021
- Runbooks-as-code: Version-controlled, auditable response procedures
Best for: Teams wanting structured, checklist-driven incident response where the runbook enforces consistency.
Comparing pricing models and hidden costs
In our experience selling to hundreds of security teams, the number one question we get after feature demos is: "What are the hidden costs?" Security features are often gated behind "enterprise" tiers, and on-call capabilities frequently cost extra.
| Platform | Private incidents | Immutable timeline | SIEM integration | Base pricing (100 users/year) |
|---|---|---|---|---|
| **incident.io Pro** | Native | Automated | Native Datadog/Splunk | $30,000 (response only) |
| **incident.io Pro + On-call** | Native | Automated | Native Datadog/Splunk | $54,000 (all-in) |
| PagerDuty | Via Slack | Editable | 370+ native tools | $72,000-96,000 |
| Jira Service Mgmt Premium | Complex schemes | Manual entry | Manual | $57,000-60,000 |
| Rootly | Granular RBAC | Unalterable | Native + webhooks | Custom pricing |
| FireHydrant | Not documented | Structured only | Limited | Custom pricing |
incident.io publishes clear per-user pricing. Pro costs $25/user/month and includes private incidents. On-call scheduling adds $20/user/month (real total: $45/user/month or $54,000/year for 100 users).
PagerDuty doesn't publish pricing publicly. Based on customer reports, full-featured incident management with AI and advanced features typically costs $60-80/user/month or $72,000-96,000/year for 100 users.
Jira Service Management uses Atlassian's standard model. According to pricing comparisons, Premium costs approximately $47-53/agent/month or $57,000-64,000/year for 100 users.
Rootly and FireHydrant both require sales contact for pricing. Enterprise features including RBAC and compliance workflows are gated behind higher tiers.
How to evaluate AI capabilities
You face a critical question when evaluating AI claims: Is the AI actually investigating the incident, or is it just autocompleting sentences based on generic patterns? For forensic postmortems, AI must cite its sources and link claims to specific timeline events.
We designed our AI SRE to connect dots between code changes, alerts, and past incidents. When it spots the likely pull request behind the incident, it links directly to the specific commit. When Scribe transcribes your call and notes "We decided to roll back to version 2.4.1," that decision appears in the timeline with timestamp and speaker attribution.
"The AI assistance with updating summary is splendid, I'm looking forward to more customization options there and also when generating postmortems." - Fina M. on G2
Here's how to test AI quality during your trial: Run 3-5 real incidents. Export the auto-generated postmortems. Check whether the AI cites specific timeline events or makes generic claims. If you see "The incident was caused by a deployment issue" without linking to the actual deploy, the AI is autocompleting, not investigating.
PagerDuty offers AI for alert correlation and prioritization using machine learning to analyze patterns. The focus is reducing noise, not autonomous investigation.
Rootly's AI surfaces similar historical incidents and suggests responders who've handled similar issues before. The AI is pattern-matching focused rather than autonomous investigation.
Evaluation criteria for security AI:
- Source citation: Does the AI link claims to specific logs, alerts, or timeline events?
- Methodology transparency: Is it analyzing actual system data or autocompleting based on word patterns?
- Forensic auditability: Can you show an auditor how the AI reached its conclusion?
- Human oversight: Does the AI suggest or does it automatically take action?
Evaluate AI capabilities by testing specific claims. Ask vendors: What exact data sources does your AI analyze? How much time does it save on specific tasks? For example, a system that "drafts postmortems from captured timeline data, reducing editing time from 90 to 15 minutes" provides testable, measurable outcomes you can verify with a pilot.
Making the business case: ROI for your VP engineering
You need ammunition for your VP Engineering. Here's the math that gets budget approval, based on what we've seen work with hundreds of teams your size.
Engineer time savings: If your team handles 15 incidents per month and spends 90 minutes manually reconstructing each postmortem, that's 22.5 hours monthly. At $150 loaded engineer cost, that's $3,375/month or $40,500/year in pure documentation labor. Automated postmortem generation reduces this significantly, reclaiming engineering hours for proactive security work.
Tool consolidation: Many teams cobble together PagerDuty (alerting) + Slack (communication) + Jira (tracking) + Confluence (postmortems) + Statuspage (customer updates). We offer good-enough versions of all five in one platform, eliminating integration maintenance and data synchronization headaches.
Risk reduction: A compliance violation from improper incident data handling can cost $50,000-500,000+ in fines and remediation. SOC 2 compliance and automated audit trails reduce this risk materially.
We've seen this exact pitch secure budget approval in 8-12 weeks across hundreds of customers. The key is showing both direct savings (tool costs) and indirect savings (engineer time) with specific monthly breakdowns your CFO can audit.
Moving forward
Ready to see how automated forensic capture eliminates the 90-minute reconstruction tax while maintaining chain of custody? Schedule a demo with our team to see timeline capture, Scribe call transcription, and AI-drafted postmortems work together to create audit-ready documentation automatically. We'll discuss your specific enterprise requirements including SAML/SCIM and compliance support for SOC 2, HIPAA, or FedRAMP.
Key terminology
Incident forensics: The process of preserving and analyzing incident data (logs, timelines, decisions) to determine root cause, liability, and compliance requirements. Requires immutable evidence and chain of custody.
Chain of custody: Chronological documentation tracking who handled evidence, when it was collected or transferred, and why. Critical for legal and compliance investigations. Automated capture is superior to manual reconstruction.
RBAC (role-based access control): Security method restricting access based on user roles within an organization. Essential for limiting who can view sensitive security incidents.
SIEM (security information and event management): Software providing real-time analysis of security alerts from applications and network hardware. Integration with postmortem tools ensures forensic accuracy by capturing system state automatically.
SOC 2 type II: Compliance standard verifying service organizations manage data to protect client interests and privacy over time. Requires audited security controls including access management and audit logging.
Private incidents: Incidents restricted to invited members only, preventing company-wide visibility of sensitive security events. Critical for data breaches, credential compromises, and compliance investigations where forensic data must be contained.
Immutable timeline: Incident record where events cannot be modified after creation. Provides forensically sound evidence with timestamps and attribution that satisfy auditors and legal requirements.
FAQs

See related articles

Customers over control: how we measure On-call reliability
Instead of thinking about reliability as an exercise in figuring out what we can control, and ignoring anything beyond that, we think about what we'll be really proud to offer to customers.
 Mike Fisher
Mike Fisher
Engineering teams in 2027
A forward look at where engineering teams are heading with AI, based on conversations with design partners who are visibly six-to-twelve months ahead of the average. Tailored code agents, MCP gateways, agentic products that talk to each other — most of the picture is already there in pockets, and the rest of the industry is closing the gap fast.
 Lawrence Jones
Lawrence Jones
incident.io launches PagerDuty Rescue Program
incident.io just launched the PagerDuty Rescue Program, making it easier than ever for engineering teams to ditch their decade-old on-call tooling. The program includes a contract buyout (up to a year free), AI-powered white glove migration, a 99.99% uptime SLA, and AI-first on-call that investigates alerts autonomously the moment they fire.
 Tom Wentworth
Tom WentworthSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization



