Best Opsgenie alternatives for compliance and security teams in 2026
Updated February 20, 2026
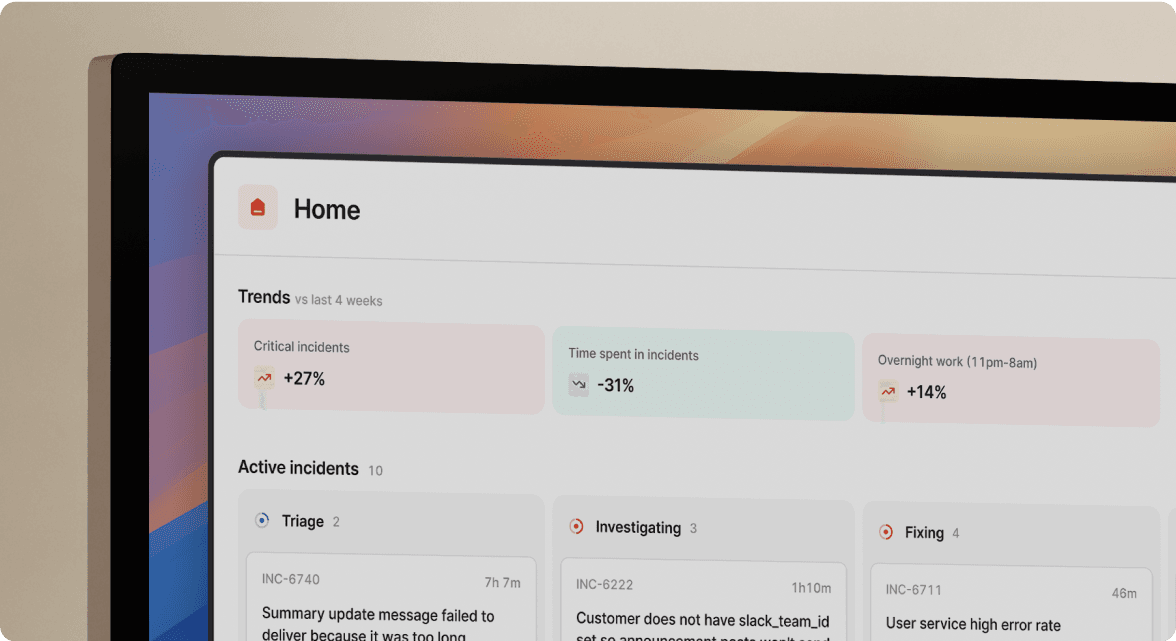
TL;DR: If your security or compliance team depends on rigorous audit trails and private incident workflows, the Opsgenie sunset (April 5, 2027) is your chance to upgrade to a platform where compliance is automated, not bolted on. We built incident.io with native private incidents in Slack, auto-generated immutable audit trails from timeline data, and enterprise-grade access controls (SAML/SCIM) that satisfy CISOs while keeping SREs productive. Teams documented in this ROI comparison achieve up to 80% reduction in MTTR through automated coordination. PagerDuty delivers battle-tested alerting with SOC 2 compliance but requires expensive add-ons and lacks Slack-native private channels. Jira Service Management is the default migration path but often creates UI complexity that slows down incident response when seconds matter.
If a SOC 2 auditor asked to see the complete timeline of your last security breach right now, could you produce it in five minutes? Or would you spend three days reconstructing events from scattered Slack DMs, PagerDuty alert history, and half-remembered Zoom calls?
For security and compliance teams evaluating Opsgenie alternatives, the April 5, 2027 sunset is forcing a migration. It's an inflection point to re-evaluate whether your incident management stack actually supports the audit trails, access controls, and private workflows that regulated industries demand.
The reality: you don't have to choose between developer velocity and strict security. Modern incident management platforms automate compliance through immutable audit trails captured during the incident, not reconstructed weeks later when memories fade.
Why the Opsgenie sunset is a security inflection point
Atlassian requires customers to migrate existing Opsgenie data and configurations before April 5, 2027, with Opsgenie end of sale effective June 4, 2025. You can no longer purchase or sign up for new Opsgenie accounts. The default migration path leads to Jira Service Management or Compass, but we think that transition deserves scrutiny from your CISO.
Security incidents have different requirements than standard outages:
- Public incidents work for site outages: A database performance issue can happen in a public Slack channel where your entire engineering team learns and contributes
- Security requires restricted access: A data breach, credential leak, or HIPAA violation needs locked-down channels where only authorized security engineers see sensitive details
- Wrong tools create shadow incidents: If your platform treats all incidents the same, teams handle sensitive issues in Slack DMs where the audit trail disappears
We've seen teams handle this migration as a chance to demand better from their tooling: automated audit trails instead of manual Google Docs, granular access controls instead of all-or-nothing permissions, and private incident workflows that keep sensitive data locked down while maintaining rigorous documentation.
The 5 non-negotiable security features for modern incident management
SOC 2 and GDPR compliance
What "certified" actually means: Your auditors will ask for the actual SOC 2 report, not just a badge on a website. They'll want to see the Data Processing Agreement (DPA) that outlines GDPR compliance, data retention policies, and sub-processor lists.
What we provide: We maintain SOC 2 Type I certification and provide a GDPR-compliant DPA that includes compliance with both EU GDPR 2016/679 and UK GDPR. We encrypt data using AES-256 and safeguard passwords using SHA-256 cryptographic hash functions.
What competitors provide: PagerDuty maintains SOC 2 Type 2 Reports with data centers complying with ISO 27001 and PCI DSS. Atlassian has obtained SOC 2 Type II reports for the Atlassian Platform, encompassing Jira Cloud, Confluence Cloud, Opsgenie, and Jira Service Management.
Enterprise-grade access control (SAML/SCIM)
Automating user provisioning and deprovisioning through SCIM ensures former employees lose access to incident data instantly when they leave the company. Manual offboarding creates compliance risk.
Our approach: We offer SAML SSO and SCIM provisioning on the Enterprise plan, with organizations on newer Pro plans also able to enable SSO using SAML. This integrates with identity providers like Okta and Azure AD to maintain least-privilege access.
What this solves: When an employee leaves, your IDP automatically removes their access across all integrated systems. No manual cleanup. No lingering permissions. No compliance gaps during audits.
Private incident channels for sensitive data
The ability to lock down a channel for a data breach, credential leak, or security vulnerability is non-negotiable. Public incident channels work for site outages. Security incidents require restricted access.
We support private alerts and escalations to restrict visibility to specific teams and individuals, with private alerts keeping any resulting escalations or incidents private as well. You can enable private capabilities from Settings > Security and select "Only invited users (private)" when declaring an incident.
Workspace owners and Slack Workspace owners maintain access to all private incidents for governance purposes, even those they're not actively invited to. This balances security isolation with administrative oversight.
Immutable audit trails and automated post-mortems
Manual Google Docs fail audits because they're editable. Someone can change the timeline, delete decisions, or "clean up" what actually happened. Immutable audit trails capture what occurred without the ability to alter the record retroactively.
We automatically generate incident timelines from Slack activity, with the narrative of the incident captured in timeline form. We don't store chat message content on our servers; we store the message ID and request content from Slack when serializing the response, as detailed in our security FAQs. This creates comprehensive monitoring and logging capabilities with immutable audit trails showing who accessed what data and when.
"incident.io makes incidents normal... I really love the slack integration, the automated summaries and the On Call pay reports feature." - Verified user on G2
Data residency and encryption standards
For organizations operating in the EU or handling data subject to GDPR, choosing where data physically resides matters. Some regulators require data to stay within specific geographic boundaries.
Our data hosting: We host transactional data in GCP's Belgium region (europe-west1), with analytical data stored within Europe. We encrypt data at rest in both our PostgreSQL database (hosted and managed by GCP) and in GCP's BigQuery platform using AES-256 encryption.
Top Opsgenie alternatives compared for security teams
incident.io: Best for automated compliance and Slack-native workflows
We built incident.io specifically for security-conscious teams who need private incidents, automated audit trails, and enterprise-grade access controls without leaving Slack.
Our security strengths:
- Private incidents in Slack: We let you create locked-down channels for security issues where only invited members see data, maintaining end-to-end privacy from alert to resolution
- Auto-generated audit trails: Our timeline captures data automatically from Slack activity, creating immutable records without manual effort
- Granular RBAC: We provide Role-Based Access Control that works natively in Slack, with SAML/SCIM on Enterprise and Pro plans
- SOC 2 certified: We maintain full compliance documentation including our DPA for GDPR
- EU data residency: We host your data in Belgium (europe-west1) for European regulatory compliance
The Intercom engineering team migrated from PagerDuty and Atlassian Status Page to incident.io in a matter of weeks, citing the Slack-native approach as the key differentiator. For Bud Financial, a fintech company navigating strict regulation, we replaced their internal Slackbot and transformed how they managed incidents in a compliance-heavy environment.
Who we're best for: SRE teams at 50-500 person companies running microservices who need to satisfy CISO requirements while keeping engineers productive in Slack.
Pricing consideration: SAML/SCIM available on Enterprise plan, with newer Pro plans also supporting SAML SSO.
PagerDuty: Best for traditional IT operations with complex alerting
PagerDuty delivers battle-tested alerting with strong compliance credentials, but the legacy architecture and pricing model create friction for modern cloud-native teams.
Security strengths:
- SOC 2 compliance: Well-established with ISO 27001 and PCI DSS data center compliance
- SAML 2.0 and OAuth: Integration with leading SSO providers including Okta, Ping, and OneLogin
- Incident timeline: Captures events during incident response for audit purposes
Limitations for security teams:
- No native Slack private incidents: Standard access controls exist but workflow isn't natively integrated into Slack with privacy isolation
- Legacy UI complexity: Complex permissioning that often requires expensive add-ons for full functionality
- Higher total cost: Per-seat pricing plus add-ons for advanced security features increase TCO
Who it's best for: Teams with complex, multi-vendor alerting requirements across diverse infrastructure who need deep integration with legacy monitoring systems.
Jira Service Management: The default migration path
Jira Service Management is the natural path for existing Atlassian customers, offering tight integration with Jira workflows, but the UI complexity creates challenges.
Security strengths:
- SOC 2 for Atlassian Platform: Annual audits with reports maintained on a rolling 12-month cycle
- SAML/SCIM via Atlassian Access: Available as a separate product across all Atlassian Cloud products
- Data residency options: Ability to select regional hosting locations including the EU
Limitations for security teams:
- Requires Atlassian Access: SAML/SCIM not included in base JSM plans; requires additional licensing
- UI complexity: Often requires heavy configuration for strict compliance workflows
- Fragmented workflows: Incident data spreads across Jira tickets, Confluence pages, and Slack threads without unified timeline
Who it's best for: Teams already heavily invested in the Atlassian ecosystem (Jira, Confluence, Bitbucket) who prioritize integration depth over ease of use.
| Feature | incident.io | PagerDuty | Jira Service Management |
|---|---|---|---|
| SOC 2 certification | Yes | Yes | Yes (Atlassian Platform) |
| Private incidents | Native Slack channels | Standard access controls | Jira security schemes |
| SAML/SCIM | Enterprise + Pro plans | Enterprise/Business tier | Atlassian Access (separate) |
| EU data residency | Belgium (Europe-west1) | Available | Available |
| Transparent pricing | Published online | Enterprise = "Contact sales" | Complex Atlassian licensing |
Deep dive: How to manage private security incidents in Slack
Here's how the private incident workflow works when you need restricted access:
- Enable private incidents: Your admins opt-in to Private Streams from Settings > Security
- Declare the incident: You use /inc commands in Slack or create through the dashboard
- Select privacy level: You see a dropdown labeled "Who should be able to see this incident?" and select "Only invited users (private)"
- Auto-restrict access: We create a private Slack channel where only invited security engineers can see the conversation, timeline, and data
- Maintain audit trail: We capture all actions in the private channel in an immutable timeline for compliance
- Manage access: You use the "Manage Access" button to grant or revoke access, with invited users automatically added to the stream Slack channel
You can also convert a public stream into a private one by making the #inc-... channel private from Slack if the incident escalates in sensitivity.
The key benefit: Sensitive data stays locked down to authorized personnel while still maintaining the complete audit trail that auditors demand. No manual Google Docs. No decisions lost in DMs. No compliance gaps.
How to evaluate vendors for SOC 2 and GDPR compliance
When evaluating incident management platforms, ask vendors these specific questions:
Access control verification:
- Do you support SCIM for automatic user deprovisioning when employees leave?
- Can we enforce MFA through our identity provider (Okta, Azure AD)?
- What RBAC granularity do you offer beyond admin/user roles?
Data handling transparency:
- Can we host data in the EU for GDPR compliance?
- Show me your sub-processor list (third parties who touch our data)
- What is your data retention policy and can we configure it?
Audit readiness:
- Will you share your SOC 2 report during evaluation?
- Do you provide immutable audit logs showing who accessed what data and when?
- How do you handle data deletion requests under GDPR Article 17 (right to erasure)?
Warning signs that should raise concerns:
- Vendors who won't share compliance reports during evaluation
- Lack of SCIM support (manual user management creates security gaps)
- Vague answers about data residency ("we use AWS" isn't specific enough)
- No DPA template available for GDPR compliance
In our experience working with fintech and healthcare customers, we've found that organizations with more than 200 people navigating regulation (fintechs), high uptime requirements (ecommerce), or complex operational domains (food delivery and logistics) benefit most from automated compliance capabilities.
Migration guide: Moving from Opsgenie without breaking compliance
Migrating incident management platforms during active security operations requires a methodical approach that maintains compliance throughout the transition.
Week 1: Audit existing users and roles
- Export current Opsgenie user list and team assignments
- Map users to roles (admin, responder, read-only) for the new platform
- Clean up dormant accounts before migration to maintain least-privilege access
- Document any custom escalation policies that need recreation
Week 1-2: Map Opsgenie teams to IDP groups
- Connect your identity provider (Okta, Azure AD) via SCIM
- Create groups in your IDP that mirror incident response teams
- Test auto-provisioning by adding/removing test users
- Verify deprovisioning removes access within expected timeframe
Week 2-4: Parallel run to verify audit logs
- Run both Opsgenie and the new platform simultaneously during transition
- Handle a few non-critical incidents in the new platform
- Verify timeline data captures all required audit trail elements
- Confirm exported post-mortems meet compliance documentation standards
We provide tools to make migrating from Opsgenie easier, with migration utilities that help transfer existing configurations.
Week 3-4: Security validation
- Test private incident creation for security scenarios
- Verify only authorized users can access private channels
- Confirm audit logs show complete timeline of access and actions
- Run a tabletop exercise simulating a security breach in the new platform
Week 4-6: Full cutover
- Migrate remaining teams to the new platform
- Redirect alerting integrations (Datadog, Prometheus) to new endpoints
- Archive Opsgenie data according to retention policies
- Update runbooks and documentation with new procedures
Don't just swap tools, upgrade your security posture
The Opsgenie sunset forces a decision: migrate to the default option or use this moment to demand better security and compliance from your incident management platform.
You don't have to choose between speed and security. The best security tool is the one your engineers actually use. If your platform makes it easier to handle sensitive incidents in Slack DMs than through the official process, you've created a compliance nightmare. We automate the boring compliance work (audit trails, post-mortem documentation, access controls) so your SREs can focus on reliability while your CISO sleeps soundly knowing the audit trail is complete.
Ready to see how private incidents and automated audit trails work in practice? Schedule a demo to walk through security-specific workflows with our team.
Key terminology
SCIM: System for Cross-domain Identity Management automates user provisioning and deprovisioning, ensuring former employees lose system access instantly when removed from the identity provider.
SAML: Security Assertion Markup Language enables single sign-on (SSO) by allowing employees to authenticate once through their identity provider and access multiple systems without separate passwords.
SOC 2: An audit report verifying that a service organization has implemented security controls and operated them effectively over time, providing evidence for third-party risk assessments.
Private incident: An incident response workflow contained within an access-restricted environment (like a private Slack channel) to protect sensitive information while maintaining an immutable audit trail for compliance purposes.
FAQs

See related articles

Engineering teams in 2027
A forward look at where engineering teams are heading with AI, based on conversations with design partners who are visibly six-to-twelve months ahead of the average. Tailored code agents, MCP gateways, agentic products that talk to each other — most of the picture is already there in pockets, and the rest of the industry is closing the gap fast.
 Lawrence Jones
Lawrence Jones
incident.io launches PagerDuty Rescue Program
incident.io just launched the PagerDuty Rescue Program, making it easier than ever for engineering teams to ditch their decade-old on-call tooling. The program includes a contract buyout (up to a year free), AI-powered white glove migration, a 99.99% uptime SLA, and AI-first on-call that investigates alerts autonomously the moment they fire.
 Tom Wentworth
Tom Wentworth
Humans aren’t fast enough for 4 9’s
Hitting 99.99% isn't a faster version of what you already do. It's a different problem to be solved: autonomous recovery, dependency ceilings, redundancies, and the discipline to build systems that buy you 15-30 minutes before you're needed at all.
 Norberto Lopes
Norberto LopesSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization



