New: AI-native post-mortems are here! Get a data-rich draft in minutes.
Postmortem software security: SOC 2, GDPR guide for SREs
Updated February 16, 2026
TL;DR: Your post-mortems contain PII, unpatched vulnerabilities, and system failure blueprints. You need encryption standards (AES-256 at rest, TLS 1.2+ in transit) equal to your production environment. Require SOC 2 Type II certification (not just Type I snapshots) to validate controls over time. For GDPR compliance, look for EU data residency options and contractual Right to Erasure support. Purpose-built incident management platforms like incident.io (which maintains SOC 2 certification) offer Slack-native workflows with Private Incidents, SAML/SCIM integration, and zero-retention AI policies. Use the evaluation checklist below to vet vendors with your CISO and pass security review on the first attempt.
Why post-mortem security is a critical vulnerability vector
You found an incident management tool your team actually likes. The Slack-native workflow clicks immediately. In your pilot, MTTR appears to drop by around 30%. Then your CISO sees "Slack bot" in the procurement request and kills the deal.
This scenario plays out weekly in 200-500 person engineering orgs. Think about your last critical incident. The post-mortem likely detailed the vulnerable endpoint, the misconfigured authentication logic, the database query pattern that caused the cascade failure, and customer data from support tickets. You just created a map for attackers. Your post-mortems contain PII including names, email addresses, phone numbers, root cause analysis exposing unpatched vulnerabilities, internal system details like IP addresses and configuration data, and code snippets shared during troubleshooting.
According to IBM's 2024 cost of a data breach report, the global average breach cost reached $4.88 million, a 10% increase from 2023. Healthcare breaches cost $9.77 million per incident. Stolen or compromised credentials were the most common initial attack vector in 2024, taking nearly 10 months to identify and contain.
The "internal leakage" problem is real. If you store post-mortems in a Google Doc with company-wide read access or a Confluence page inheriting broad space permissions, you've essentially published your organization's weaknesses to every employee, contractor, and intern. As NIST explains, the same information that seems innocuous in one context becomes highly sensitive in another.
You need tools that give you granular control over data visibility for sensitive scenarios. By default, incident.io makes all incidents transparent across your organization, a deliberate design choice that encourages learning and collaboration. However, incident.io's private incidents feature provides an explicit opt-in mechanism when handling security-critical situations. When you declare an incident as private, it remains visible only to explicitly invited team members. Note that workspace owners maintain access to all incidents for administrative purposes, but you can restrict visibility from the broader engineering organization.
Here's the security framework you need to evaluate modern incident management tools and pass CISO review on the first attempt.
Core compliance standards: SOC 2 Type II and ISO 27001
You need to understand the two forms of SOC 2 certification because only one gives you meaningful assurance. Type I evaluates whether controls are designed properly at a single point in time, like checking if your fire exits are marked. Type II examines how well controls perform over 6-12 months, watching to ensure people actually use those exits correctly for months. You need Type II because it proves operational effectiveness over time, not just proper design at a snapshot.
When evaluating vendors, ask for the actual SOC 2 report and check the exceptions list. Every report includes exceptions or deviations from ideal controls. Zero exceptions means exceptional processes or dishonest reporting. Look for how they remediated issues and what's covered in scope.
incident.io achieved SOC 2 certification as a deliberate priority, stating that "compliance and security have also ranked high on their list of top priorities." The company implemented continuous monitoring using Vanta to maintain security posture. For the most current certification details, review their Trust Center documentation.
ISO 27001 represents the international standard for information security management systems. While SOC 2 is US-focused, ISO 27001 is globally recognized and publicly certified. Organizations serving international customers often need both.
GDPR and data privacy in incident retrospectives
The GDPR places significant emphasis on data handling through stringent requirements for international data transfers. Organizations processing EU citizen data must ensure robust protection if data leaves the EU or EEA. This includes Standard Contractual Clauses or Binding Corporate Rules.
The "Right to be Forgotten" in logs presents a unique challenge: Data subjects can request deletion of personal data when it's no longer necessary, when they withdraw consent, or when data was processed unlawfully. Here's your problem: customer emails, phone numbers, or account identifiers frequently appear in log snippets pasted into Slack channels during troubleshooting. An engineer debugging an authentication failure might paste a log line containing a customer's email address. That PII now exists in your incident timeline. When that customer exercises their right to erasure, can you actually find and remove every instance?
GDPR emphasizes data minimization: collect and process only the data necessary for stated purposes. For post-mortems, question whether you need to retain full log dumps with PII or if sanitized versions showing the failure pattern would suffice.
incident.io's Data Processing Agreement states they comply with GDPR, UK GDPR, and the Data Protection Act 2018. When engaging subprocessors, they require written agreements to process Personal Data only in countries the EU has declared to have adequate protection levels or using Standard Contractual Clauses. For organizations with EU data storage requirements, work directly with incident.io to configure your specific data residency needs. For GDPR implementation specific to your organization's data flows and regulatory requirements, work with your legal counsel to interpret these requirements for your specific use case.
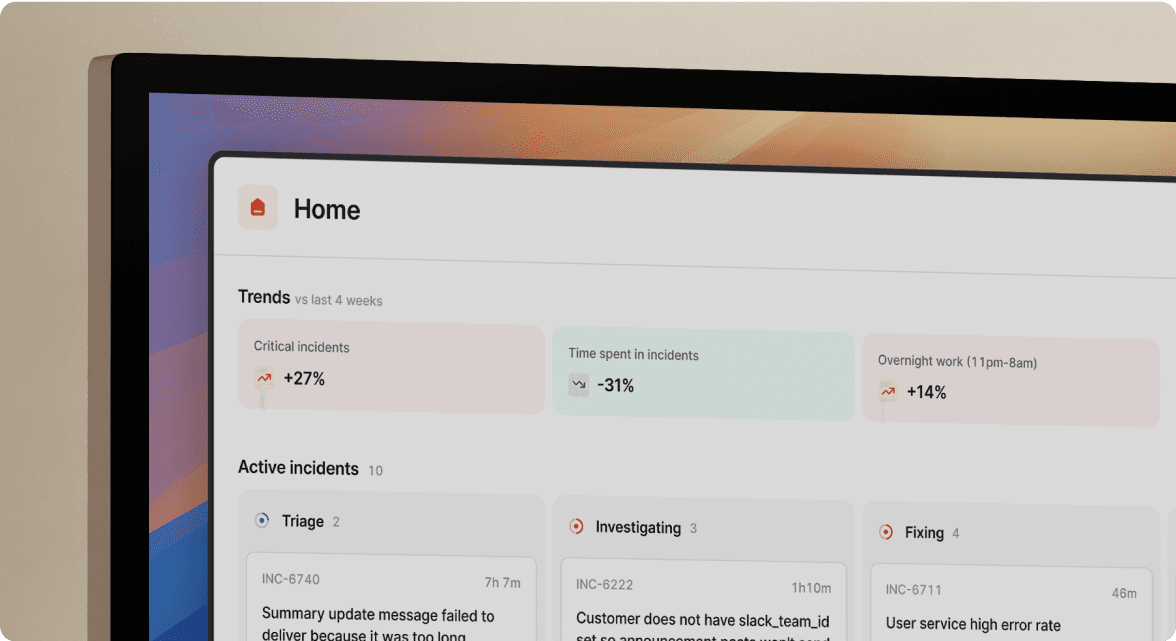
"Incident.io helps promote a blameless incident culture by promoting clearly defined roles... We have also started using it to conduct game days... The incident dashboard is probably my favourite feature of the tool." - Saurav C. on G2
Data encryption and handling: At rest, in transit, and in logs
You need non-negotiable baseline encryption specifications for any enterprise SaaS. All modern platforms should use at least TLS 1.2, with TLS 1.3 preferred. NIST recommends TLS 1.2 as the minimum acceptable version for data in transit. For data at rest, AES-256 offers the highest degree of security and is the gold standard. Security-conscious organizations require AES-256 for all stored data.
TLS 1.2 and TLS 1.3 use AES cipher suites to encrypt network traffic, providing the same cryptographic strength for data in transit that AES-256 provides for data at rest. Your post-mortem data is protected both when moving between systems and when stored on disk.
The Slack-native nuance: This is where many security teams get nervous. "If the incident management tool lives in Slack, doesn't that mean our sensitive data lives in Slack's infrastructure?" We built incident.io to use API-based data capture with separate secure storage infrastructure. The platform captures data from Slack via APIs, then processes and stores structured incident data (timelines, postmortem fields, decisions) in our own secure, encrypted database. The Slack channel serves as the collaboration interface, but the permanent record lives on infrastructure subject to our SOC 2 controls.
This architecture provides critical security benefits: data at rest encryption under vendor control independent of Slack's security model, granular RBAC independent of Slack permissions, all stored data under the vendor's compliance certifications, and the ability to enforce data handling policies through the vendor platform. The Slack-native experience is about user interface and workflow, not data storage location.
"For our engineers working on incident, the primary interface for incident.io is slack... But back in the days, we had a process... That's where incident.io really shines: it allows to seamlessly nudge or suggest actions." - Alexandre R. on G2
Access controls, audit trails, and role-based permissions
When you manage users manually, you create a dangerous security gap. When employees leave your organization, their access needs immediate removal across all systems. SAML enables single sign-on so users enter credentials once to access multiple systems, reducing password fatigue and reuse risk. SCIM automates user provisioning and deprovisioning as employees join, move, or leave.
The critical benefit: automatic deprovisioning. Without SCIM integration, you manually update access across multiple tools when engineers leave. In the chaos of an unexpected departure, this process gets delayed by days or weeks, leaving former employees with access to sensitive post-mortem data. SAML answers "Are you really you?" while SCIM answers "Should you have access?" Together they automate the complete identity lifecycle: SAML verifies user credentials once, while SCIM instantly provisions access when employees join and revokes it when they leave.
Role-Based Access Control goes beyond simple read/write permissions: Effective RBAC should distinguish between incident participants who need full access, observers who need visibility into trends, security teams who need access to private security incidents, and auditors who need read-only access to completed post-mortems.
Immutable audit logs transform security investigations: An immutable audit log is a cryptographically protected, append-only record where past entries cannot be altered or deleted without detection. The primary benefit is trust. Instead of wondering what happened during a data breach, you have a definitive record. Forensics requires logs with sufficient fidelity to reconstruct timelines, identify actors, and correlate events.
Immutability means tamper-resistant: once information is written, it cannot be altered or deleted by anyone, including system administrators. For post-mortem platforms, this means logging post-mortem creation and edits, access events showing who viewed sensitive data, permission changes to incident records, and export actions.
AI security: Ensuring automated analysis doesn't leak data
"Will your AI train on my data?" This question stops many AI-powered tool evaluations. The legitimate concern: if your incident platform uses AI to generate post-mortem summaries, does your proprietary code and vulnerability data get ingested into a public LLM?
The enterprise standard is zero data retention (ZDR) policies. Salesforce's Einstein Trust Layer prevents LLM partners from retaining any customer data including prompts and responses. The model forgets the prompt as soon as the response returns. These platforms use ZDR endpoints that process prompts in volatile memory, discarding inputs and outputs instantly.
incident.io's terms specify customer data is used solely to provide AI features, not to train public models. AI features are disabled by default in private incidents, though you can opt-in with explicit consent.
When evaluating vendors, ask specifically: Do you use zero-retention API endpoints? Can you provide written confirmation customer data won't train public models? Can we disable AI features for sensitive incidents?
"Clearly built by a team of people who have been through the panic and despair of a poorly run incident... Everything integrates seamlessly around Slack... They also provide great insights into the data behind your incidents." - Rob L. on G2
Evaluation checklist: How to vet post-mortem tools for security
Use this checklist during vendor procurement to systematically evaluate security posture:
Compliance and certification:
- SOC 2 Type II report (verify 6-12 month audit period, not Type I)
- ISO 27001 certification for international operations
- GDPR compliance with DPA including Standard Contractual Clauses
- Industry-specific compliance: HIPAA (healthcare), PCI DSS (payments)
Data encryption and handling:
- TLS 1.2 minimum (TLS 1.3 preferred) for data in transit
- AES-256 encryption for data at rest
- Key management via reputable service (AWS KMS, Azure Key Vault)
- Data residency options (EU hosting available if required)
- Clear documentation of where data is stored
Access controls and authentication:
- SAML/SSO support for centralized authentication
- SCIM support for automated user provisioning and deprovisioning
- Granular Role-Based Access Control beyond simple admin/user roles
- Private or restricted incident types for sensitive security issues
- Multi-factor authentication enforcement options
Audit and forensics:
- Immutable audit logs showing who accessed what data and when
- Change tracking for post-mortem edits with full version history
- Export capabilities for compliance reporting
AI and data usage:
- Written policy on customer data usage for AI features
- Zero-retention or explicit no-training guarantees for public LLMs
- Ability to disable AI features selectively or entirely
Vendor security practices:
- Penetration testing conducted regularly (annual minimum)
- Bug bounty program or vulnerability disclosure process
- Security questionnaire response available
incident.io addresses these requirements through SOC 2 certification, GDPR-compliant data processing, AES-256 encryption, SAML/SCIM on Enterprise plan, and Private Incidents for sensitive data.
How incident.io bridges usability and security
You don't trade security for usability with purpose-built incident management platforms. incident.io proves you can have Slack-native speed with enterprise-grade security.
Private Incidents for sensitive data: incident.io's incidents are public by default to promote transparency and learning. When you need privacy, for security breaches, PII exposure investigations, pre-disclosure vulnerabilities, or HR-related technical issues, you can explicitly create Private Incidents. These keep escalations and incidents private end-to-end, with only explicitly invited team members able to view the channel and post-mortem.
Enterprise access management: incident.io supports SAML/SCIM on Enterprise plan for SSO through your identity provider, automatic user provisioning when engineers join, immediate access revocation when employees leave, and MFA policy enforcement through your IdP.
incident.io achieved SOC 2 certification as a priority despite fast growth. The company counts engineering teams at Netflix, Airbnb, and OpenAI among its clients in regulated industries.
"Nobody wants to run an incident, but it's an inevibility in the software industry. Incident.io actually makes running an incident an enjoyable expierence and really helps bring focus and organization to a process that has historically been difficult to organize." - Verified user on G2
Security comparison: Homegrown vs. legacy vs. modern platforms
| Security feature | Homegrown slack bots | Legacy tools (Jira/Confluence) | Purpose-built platforms (incident.io) |
|---|---|---|---|
| SOC 2 Certification | None | Varies by vendor | Certified with continuous monitoring |
| Immutable audit logs | Rarely implemented | Basic activity logs | Tamper-evident logs |
| Private incidents | Manual access control | Complex nested permissions | Built-in privacy controls |
| SAML/SCIM | Manual user management | Often enterprise tier only | Available on enterprise plan |
| Data encryption | Depends on storage | AES-256 standard | AES-256 with managed keys |
| AI zero-retention | N/A | Unclear or no policy | Explicit no-training guarantee |
Homegrown tools built by internal teams typically lack formal security controls because they're maintained as side projects. The engineer who built your incident bot two years ago has moved teams. Breaking Slack API changes require urgent fixes. Security audit logs never got implemented.
Legacy collaboration platforms like Confluence and Jira suffer from permissive default permissions. Pages inherit space permissions, making it easy for sensitive post-mortems to become searchable by the entire company. NIST guidance explains that context determines data sensitivity. Locking down specific pages requires understanding nested inheritance and complex configuration that teams skip under time pressure.
Purpose-built incident management platforms design security into the architecture from day one rather than bolting it on after the fact.
Bringing your CISO into the evaluation
Security enables speed by removing fear. When your team trusts that sensitive post-mortems won't leak beyond intended audiences, they declare more incidents. WorkOS VP Alon Levi describes how his team gained confidence to declare more incidents because incident.io made the process safe and structured.
Your CISO isn't the enemy of good incident management. They're your partner in building systems that protect customer data while enabling rapid response. Bring them into evaluations early with the data they need: SOC 2 reports, encryption specifications, data flow diagrams, AI data usage policies, and access control documentation.
The checklist in this article gives you the framework to evaluate platforms systematically. Focus on vendors who can answer these questions with specific evidence, not marketing claims. "We take security seriously" is meaningless. "Here's our SOC 2 report showing tested controls" is actionable.
For teams ready to evaluate a platform that combines Slack-native collaboration with enterprise security, book a demo to see Private Incidents, SAML integration, and security controls in action. Bring your security team to the demo. Ask hard questions about encryption, data residency, and AI policies.
Your post-mortems are toxic assets that need protection equal to your production systems. Select tools that recognize this reality.
Key terms glossary
SOC 2 Type II: An audit report attesting to the effectiveness of a service organization's controls over a 6-12 month period, not just a point-in-time snapshot.
RBAC (Role-Based Access Control): Restricting system access to authorized users based on their organizational role, enabling granular permissions beyond simple admin/user distinctions.
SAML (Security Assertion Markup Language): An open standard for exchanging authentication and authorization data between parties, enabling single sign-on across multiple applications.
SCIM (System for Cross-domain Identity Management): A protocol for automating user provisioning and deprovisioning across different systems, critical for immediate access revocation when employees leave.
Data residency: The physical or geographic location where an organization's data is stored and processed, important for regional compliance requirements.
Immutable audit log: A cryptographically protected, append-only record of events where past entries cannot be altered or deleted without detection, providing tamper-evident forensic trails.
Zero Data Retention (ZDR): An AI processing model where prompts and responses are discarded immediately after inference, ensuring customer data is not stored for training or analytics.
FAQs

See related articles

How to migrate your paging tool without breaking your team
Migrating your paging tool is disruptive no matter what. The teams that come out ahead are the ones who use that disruption deliberately. Strategic CSM Eryn Carman shares the four-step framework she's used to help engineering teams migrate — and improve — their on-call programs.
 Eryn Carman
Eryn Carman
How Catalog changes the game for long-term maintenance
Model your organization once, and let every workflow reference it dynamically. See how Catalog replaces hardcoded incident logic with scalable, low-maintenance automation.
 Chris Evans
Chris Evans
The post-mortem problem
Post-mortems are one of the most consistently underperforming rituals in software engineering. Most teams do them. Most teams know theirs aren't working. And most teams reach for the same diagnosis: the templates are too long, nobody has time, nobody reads them anyway.
 incident.io
incident.ioSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization


