Responding to a data breach with the urgency it deserves

Data breaches are becoming increasingly common, and it’s important for businesses to know how to manage them properly. After all, they pose a major risk that businesses of all industries face, and the right response is paramount to reducing the damages.
While the risks of a data breach are significant, failing to respond quickly and properly can be even more damaging. A poorly executed response puts your customers and your business at risk of financial losses, reputational damage, or even lawsuits. That's why developing an effective data breach response plan is essential.
A lot weighs on your response to data breaches
When it comes to data breaches, time isn't on your side; you have to act swiftly and decisively in order to prevent further damage. Unfortunately, many businesses fail to respond to data breaches with the urgency that they deserve, resulting in further risks and potential harm.
The first step in a data breach response is understanding the type of threat and its related risks. Common types of risk include identity theft and reputational damage for those whose data has been breached. It is also important to consider how a data breach might impact your business, either in financial losses or legal liabilities.
A delayed response can result in fines from regulatory bodies, such as the FTC. Not to mention, if the public finds out that your business failed to handle a security incident appropriately, it could have disastrous consequences for customer trust and eventually revenue.
With all that said, it’s essential that businesses are as transparent as possible about any data breaches they experience. Customers usually respond better if they feel like the company is being honest with them about what happened and how they are dealing with it. Companies should also be proactive in informing those individuals whose data was affected by the breach so that they can take steps to protect themselves from potential harm.
Neglecting to do this out of fear of backlash will only make a bad situation much worse.
How you should respond to a data breach
Once you have identified a problem, you need to take action quickly. Listed here are eight of the data breach response best practices you should follow in order to lessen the damage of an incident.
1. Try to identify the data that has been compromised
The first step in responding to a data breach is to identify the data that has been compromised in order to get the incident response process rolling. This can include passwords, financial information, user contact information, or something else.
This process can involve examining internal systems for evidence or using forensic experts who specialize in digital forensics, data analysis, and activity tracking.
Regardless of the method, speed should be your first priority. You cannot take action without first knowing the full scope of the breach.
2. Perform a risk assessment
Once you’ve identified what information was affected by the breach, you need to perform a risk assessment in order to determine the potential harm that the loss of that information could have caused. This includes looking at factors such as how sensitive the data is, how much damage could be done if it were misused, who might be able to access it, and what remedies are available if there is misuse or theft of customer information.
This step is essential in determining how you respond next and whether additional security measures need to be implemented in order to secure any areas at risk from future data breach incidents.
3. Comply with local data breach notification laws
Depending on where your business is based, there may be specific laws or regulations that determine how you should handle data breach incidents. For example, you may be legally required to notify customers when their personal data has been breached, or required to contact law enforcement as soon as possible.
It’s important that you treat the compliance step as urgently as the breach itself. Otherwise you can soon be dealing with penalties and lawsuits in addition to fallout from the breach.
4. Hire a forensic expert to analyze any fallout from the data breach
In order to understand what happened during a breach, companies should request the help of professionals. As soon as possible following a data breach incident, it’s a good idea to bring on experts who can collect evidence relating to the breach itself.
These forensic specialists can help uncover facts such as who orchestrated the incident, and can provide insight into potential weaknesses that facilitated it in the first place. They are also able to provide valuable insights later down the line during post-incident analysis sessions with staff members or executive-level decision-makers within the company itself.
5. If you have one, get your legal team on board
Immediately following the detection of a data breach, it’s important for companies to get their legal team involved. This is because breaches often prompt legal claims against your business. After all, you have failed to protect your customers’ private information or IP rights belonging to third parties.
By involving your legal team as soon as possible, you’ll be able to ensure compliance with local laws relating to data breaches and minimize legal liability moving forward.
Working with lawyers specializing in cybersecurity law will help your organization navigate complex regulations surrounding reporting requirements. Not to mention, a lawyer can be a part of your future emergency response plan.
6. Make data breach policy reviews a recurring event
As a business that regularly handles or stores the data of customers or business partners, it’s necessary to have policies in place regarding how you’ll be handling incidents pertaining to data safety. These policies should provide clear guidance on how your organization will respond when customer information has been breached, as well as any specific steps that must be taken in different scenarios.
An up-to-date policy should cover every aspect related to data security manners. For example, how is confidential material handled online? What encryption is used to keep it secure? And what’s the procedure taken when wiping drives containing sensitive information?
7. Be proactive about making sure your incident response teams are prepared
Having a data breach incident response team always at the ready with clear procedures laid out ahead of time is essential for dealing with a security breach swiftly and effectively. Your team should be well-versed not only in your systems and databases, but also in the data security and privacy policies you have in place.
To ensure they’re always up to date, you should consider conducting regular company-wide drills, workshops, and seminars. This allows you to pinpoint any shortcomings in your response and take the appropriate steps to overcome them in time.
8. Use an incident management tool to streamline your response process
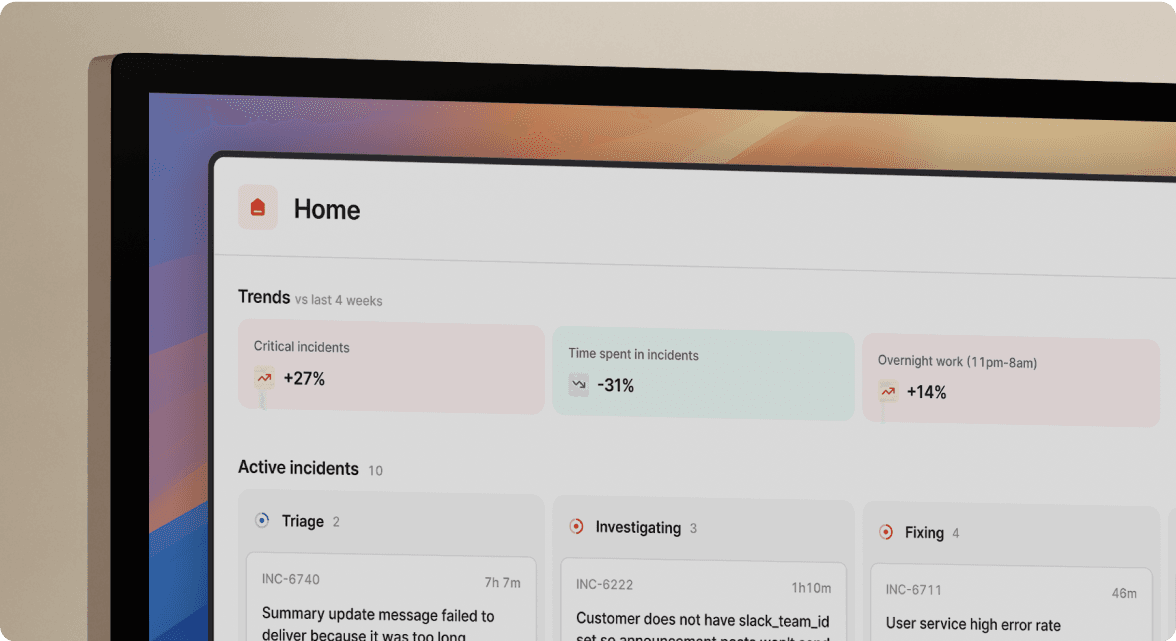
Data breaches are complex events. They require careful coordination between teams across multiple departments using dedicated incident management tools. It's important that you use software that helps simplify the processes, all the way from incident declaration down to your incident post-mortem.
This is particularly important for larger organizations, especially if you conduct operations in more than one physical location. Using specialized software enables you to unify your response across multiple networks, ensuring other branches' safety or isolation from the incident.

See related articles

Customers over control: how we measure On-call reliability
Instead of thinking about reliability as an exercise in figuring out what we can control, and ignoring anything beyond that, we think about what we'll be really proud to offer to customers.
 Mike Fisher
Mike Fisher
Engineering teams in 2027
A forward look at where engineering teams are heading with AI, based on conversations with design partners who are visibly six-to-twelve months ahead of the average. Tailored code agents, MCP gateways, agentic products that talk to each other — most of the picture is already there in pockets, and the rest of the industry is closing the gap fast.
 Lawrence Jones
Lawrence Jones
incident.io launches PagerDuty Rescue Program
incident.io just launched the PagerDuty Rescue Program, making it easier than ever for engineering teams to ditch their decade-old on-call tooling. The program includes a contract buyout (up to a year free), AI-powered white glove migration, a 99.99% uptime SLA, and AI-first on-call that investigates alerts autonomously the moment they fire.
 Tom Wentworth
Tom WentworthSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization



