Organizing an efficient incident response team

Cybersecurity threats are, unfortunately, a pervasive and ongoing concern. Given that 93% of company networks are vulnerable to breaches of some sort, experiencing a cyberattack is a matter of when, not if, for modern businesses. Because of the high risk and cost of an incident, establishing a dedicated incident response team is one of the consequential decisisons you can make.
It’s worth noting that risk profiles vary from business to business, so your cyber incident response team will as well. However, some roles are critical to all teams. Let’s dive into those here.
What are incident response teams and are they responsible for?
A cyber incident response team is a group of people responsible for responding to and managing cybersecurity incidents in a business. Their goal is to minimize damage from a cyber attack or incident and, ideally, prevent it from happening again in the future.
Incident response teams are responsible for quite a bit, but their main responsibilities boil down to:
Detecting and identifying incidents
The first and most obvious responsibilitiy: incident response teams use monitoring tools to detect active threats. They monitor system logs and network activity for abnormalities that could indicate a problem.
Containing and mitigating any incidents
Using pre-established processes and response plans, the incident response team will work to minimize the impact of the incident. They make take actions such as blocking malicious traffic and isolating affected systems to prevent the issue from spreading.
Communicating with stakeholders
Cybersecurity incidents affect the entire organization, not just the software engineering department. Because of this, a computer security incident response team will work closely with a broad range of stakeholders, including executive staff and in some extreme cases, even law enforcement.
Investigating potential incident fallout
Incident managers analyze loss incidents to determine the underlying cause, scope, and impact using various tools. The incident response plan may include analyzing system logs and network traffic as well as conducting a full forensic analysis.
Preventing future incidents
One of the most vital aspects of incident response is developing strategies to prevent future attacks. They’ll use their findings in the post-incident analysis to recommend measures to improve security and employee education as needed.
Which roles should I have on my incident response team?
An effective incident response team depends on the technical expertise of its members. Each company has a different risk profile that will affect the incident response team roles. However, most teams include at least the following:
An on-call team to effectively initiate incident responses
When you provide a crucial service that your customers rely on, you need to maintain an on-call team to respond to high-priority incidents immediately. An on-call team primarily works during off-hours, but if your engineering team has a lot of other responsibilities, it’s not a bad idea to designate an on-call team during business hours as well.
To avoid placing too much of the burden on the same people, you should alternate on-call duties among team members. This team will be the first to be notified if the event of an incident. Don’t overlook the importance of maintaining an on-call presence from roles outside of engineering. Having the right people on your on-call team is critical, so include members from executive staff, legal, marketing, compliance, and other relevant departments.
Incident leads to play role of manager
The incident lead plays a critical role on the incident response team. This role requires a trusted leader and is often a senior engineer. They’re responsible for developing and implementing the incident response plan and managing the team to ensure incidents are identified, contained, and resolved as quickly as possible.
While some technical knowledge is necessary, the lead investigator shouldn’t be working at the code level to solve the problem. They need to take a bird’s eye view to efficiently organize a response.
Communications lead to keep folks in the loop
The communications lead handles internal and external communication throughout the incident lifecycle. They’ll decide which communication channels to use to keep stakeholders, law enforcement, customers, and the public updated and informed about the incident and the team’s progress in resolving it. In today’s environment of constant contact facilitated by social media, part of your communications lead’s role will involve ensuring your social media channels are monitored, and the social media team has updated information to distribute.
If the incident is wide-ranging and complex, you may need an internal and external communications lead.
Incident response timeline lead for proper documentation
The incident response timeline lead is responsible for managing the timeline and ensuring all aspects of the incident and response are accurately documented. The timeline is a guide that will help you develop an effective post-incident response. The timeline should capture key points such as:
- Identifying the incident
- Communicating effectively with internal and external stakeholders
- Key people involved
The incident response timeline lead will provide the timeline and document the audit trail. They are in charge of making sure the timeline isn’t altered in any way and contains all of the facts about what happened at each stage.
Security analyst to effectively prevent future incidents
The security analyst’s primary responsibility is analyzing the root cause of the incident and identifying security vulnerabilities and weaknesses that contributed to the incident. They may perform activities such as a post-incident review, a risk assessment, developing new security procedures, monitoring security systems, and conducting security training.
Legal representation for issues and guidance**
The legal representative may be an in-house attorney or an outside law firm hired by the company. The legal representative will ensure that all incident response documents and procedures comply with the applicable laws, regulations, and customer obligations.
Tips for effectively optimizing your incident response team
Putting together a cyber incident response team can be a complex process, but a systematic approach can help make it more manageable.
- Define roles and responsibilities: Clearly defining the duties of each team member will help your team run smoothly and eliminate confusion during an incident.
- Provide training: Regular training sessions will keep the team’s skills sharp, ensure they understand the incident response plan, and prepare them for a real incident.
- Set up communication channels: Before an incident occurs, have communication channels in place that allow team members to quickly and effectively get in touch with each other and with other stakeholders.
- Establish relationships with external parties: Know who you need to contact in case of an incident and develop a professional relationship before a crisis occurs. This may include law enforcement, cybersecurity experts, and outside stakeholders.
- Set up automated tools: Using incident response technology can increase your response time and effectiveness. Make sure you have the tools in place in advance so your team will be familiar with them.
Give your incident response teams the tools to handle incidents effectively
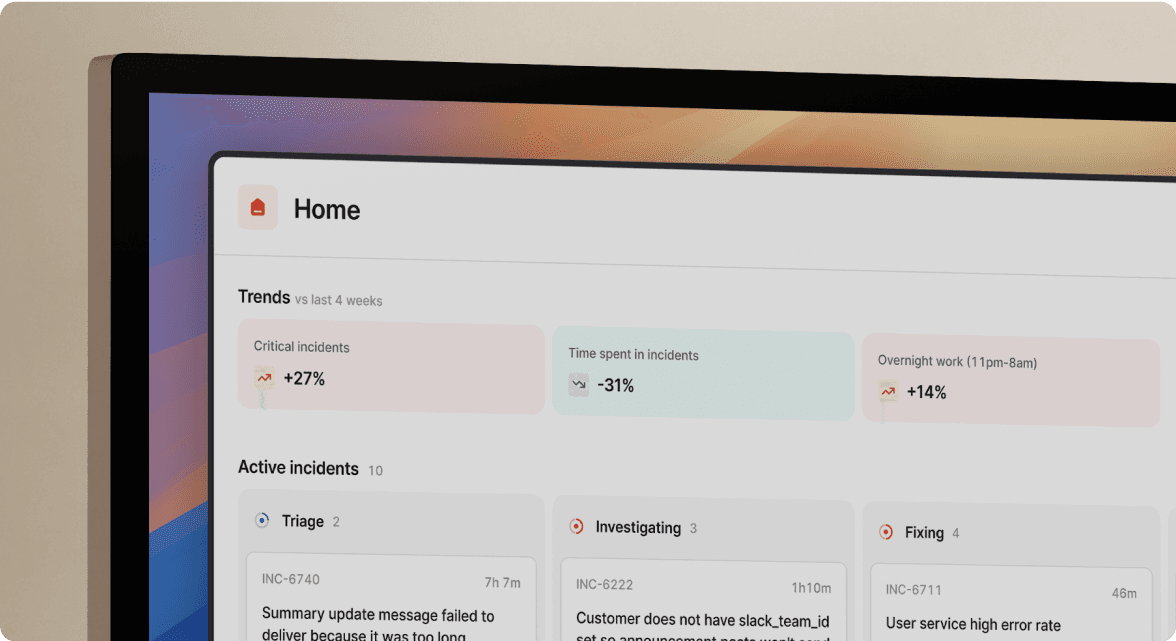
incident.io is a comprehensive incident management platform that simplifies the process for everyone on your incident response team. It helps streamline your workflow for a fast, efficient response. With incident.io, you’ll get:
- The ability to effectively manage the incident response process all from Slack
- Customizable incident workflows tailored to the needs of your organization
- Integrations with collaboration tools such as Notion, Jira, Opsgenie and Pagerduty
- An Insights dashboard to help identify trends and proactively address any areas of improvement in your incident response
Put together, incident.io gives your incident response team the tools to work efficiently, reduce response times, and conduct more insightful post-incident analysis.
Reach out to schedule a custom demo.
See related articles

Customers over control: how we measure On-call reliability
Instead of thinking about reliability as an exercise in figuring out what we can control, and ignoring anything beyond that, we think about what we'll be really proud to offer to customers.
 Mike Fisher
Mike Fisher
Engineering teams in 2027
A forward look at where engineering teams are heading with AI, based on conversations with design partners who are visibly six-to-twelve months ahead of the average. Tailored code agents, MCP gateways, agentic products that talk to each other — most of the picture is already there in pockets, and the rest of the industry is closing the gap fast.
 Lawrence Jones
Lawrence Jones
incident.io launches PagerDuty Rescue Program
incident.io just launched the PagerDuty Rescue Program, making it easier than ever for engineering teams to ditch their decade-old on-call tooling. The program includes a contract buyout (up to a year free), AI-powered white glove migration, a 99.99% uptime SLA, and AI-first on-call that investigates alerts autonomously the moment they fire.
 Tom Wentworth
Tom WentworthSo good, you’ll break things on purpose
Ready for modern incident management? Book a call with one of our experts today.
We’d love to talk to you about
- All-in-one incident management
- Our unmatched speed of deployment
- Why we’re loved by users and easily adopted
- How we work for the whole organization



