Private incident types
Create security-specific incident types that are private by default.
- Incidents are invite-only and hidden from global dashboards and feeds
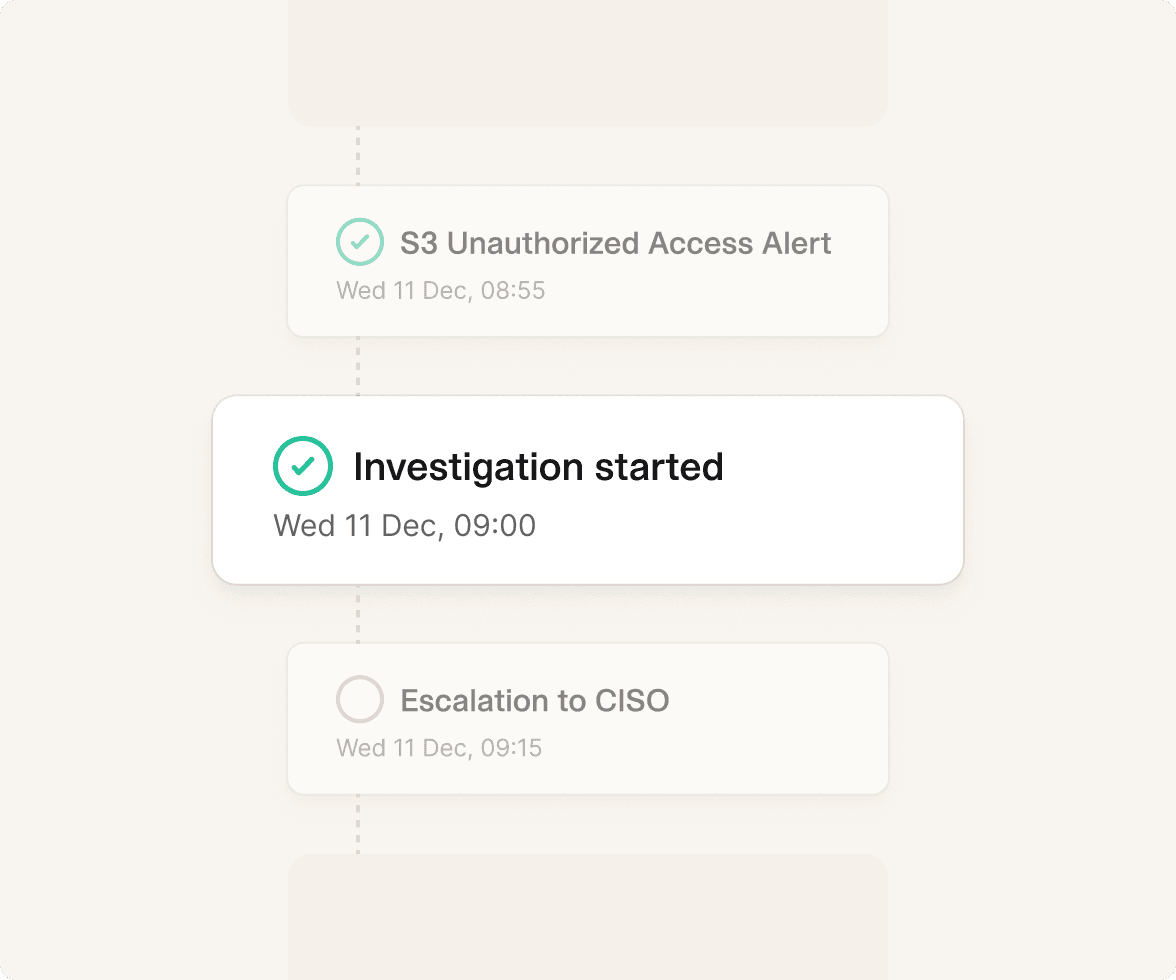
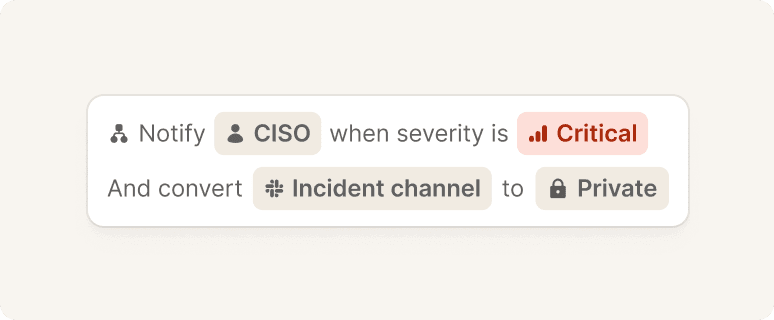
- Define custom workflows, severities, roles, and fields for security response
- Keep investigations isolated while maintaining a consistent response structure
This allows security teams to run a tailored response process without exposing sensitive context.